- Get Started with Threat Detection Management
- Analytics Rules
- Analytics Rule Classifications
- Create an Analytics Rule
- 1. Define the analytics rule
- 2. Import the analytics rule
- 3. Enable the analytics rule
- 4. Apply the analytics rule to your environment
- factFeature Analytics Rule JSON Configuration
- profiledFeature Analytics Rule JSON Configurationh
- contextFeature Analytics Rule JSON Configuration
- numericCountProfiledFeature Analytics Rule JSON Configuration
- numericDistinctCountProfiledFeature Analytics Rule JSON Configuration
- numericSumProfiledFeature Analytics Rule JSON Configuration
- Manage Analytics Rules
- Tune Analytics Rules
- Share Analytics Rules
- Troubleshoot Analytics Rules
- Analytics Rules Syntax
- Advanced Analytics Rule Syntax vs. Analytics Rule Syntax
- Logical Expressions in Analytics Rule Syntax
- String Operations Using Analytics Rule Syntax
- Integer Operations Using Analytics Rule Syntax
- Time Operations Using Analytics Rule Syntax
- Network Operations Using Analytics Rule Syntax
- Context Operations Using Analytics Rule Syntax
- Entity Operations Using Analytics Rule Syntax
- Correlation Rule Operations Using Analytics Rule Syntax
- Monitor the Analytics Engine
- Correlation Rules
- Threat Scoring
contextFeature Analytics Rule JSON Configuration
As you define your own contextFeature analytics rule, review the structure and required fields for a contextFeature analytics rule.
Let's look at an example JSON configuration for a contextFeature analytics rule:
{
"version":"1",
"ruleDefinitions": [
{
"templateId": "DM-Cntx-PC-Critical-Sniffer",
"name": "Process is a sniffing tool: True\\False",
"description": "Process is a sniffing tool: True\\False",
"applicableEvents": [
{
"activity_type": "process-create"
}
],
"detectionReason": "Process is a sniffing tool: ${trigger.value}",
"type": "contextFeature",
"mitre": [
{
"techniqueKey": "T1040",
"technique": "Network Sniffing",
"tactic": "Credential Access",
"tacticKey": "TA0006"
},
{
"techniqueKey": "T1040",
"technique": "Network Sniffing",
"tactic": "Discovery",
"tacticKey": "TA0007"
}
],
"useCase": [
"Compromised Credentials"
],
"trainOnCondition": "true",
"actOnCondition": "true",
"value": "ContextListContains('Net Sniffer Processes', toLower(process_name))",
"familyId": "process-creation-activity",
"ruleGroupId": "pc-critical-process-context-group"
}
]
}An analytics rule is a JSON object that includes two mandatory fields: version and ruleDefinitions.
version indicates the layout version. It tracks the layout version if there are any updates to the layout or the New-Scale Security Operations Platform. Currently, the version is 1.
ruleDefinitions contains one or more rule definitions. The value of ruleDefinitions is an array. The array contains an object, and each object is a rule definition. The rule definition contains the fields that define an analytics rule and how it functions. Some fields are mandatory for the analytics rule to function while other fields are optional.
Ensure you include all necessary fields for your analytics rule to work as you expect and ensure all field values meet the requirements for a contextFeature rule:
Field | Description | Mandatory or Optional | Value Requirements |
|---|---|---|---|
templateId | A unique identifier associated with the analytics rule. | Mandatory |
|
name | The analytics rule name. | Mandatory |
|
description | A description of the analytics rule. | Optional |
|
applicableEvents | The type of events the analytics rule evaluates. | Mandatory |
|
detectionReason | A dynamic name describing the rule and why it triggered on a specific event. It elaborates on the 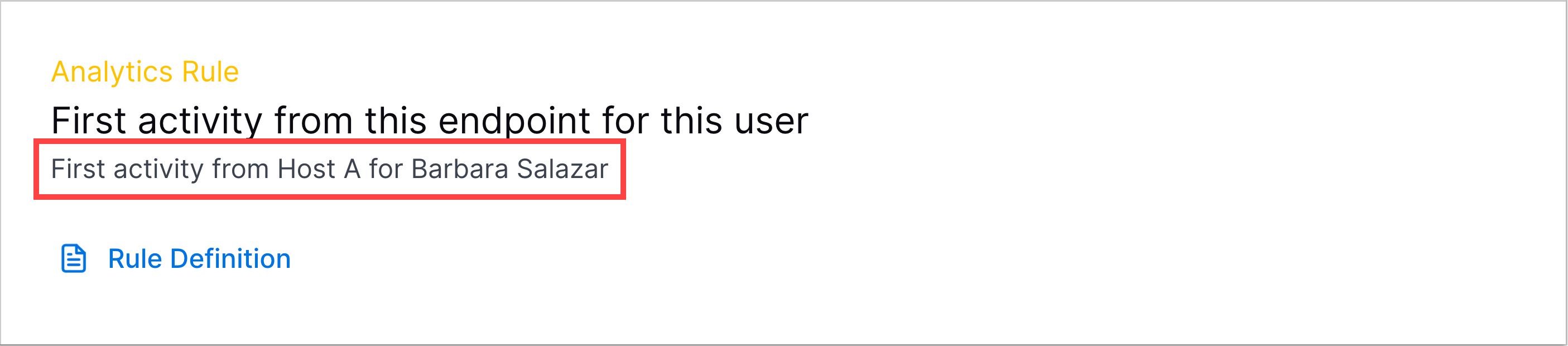 | Mandatory |
|
type | The analytics rule type. | Mandatory |
|
mitre | The MITRE ATT&CK® tactics and techniques associated with the analytics rule. | Optional |
|
useCases | Exabeam use case associated with the analytics rule. | Optional | Must be an array of strings. Each string must be an existing Exabeam use case:
|
trainOnCondition | The events on which the analytics rule trains. | Optional |
|
actOnCondition | A high-level filter for the events on which the analytics rule triggers. | Optional |
|
value | The specific piece of context data the analytics rule identifies. | Mandatory |
|
scopeValue | The event field on which the model for the analytics rule trains; typically an object or entity. | Mandatory |
|
scoreUnless | A list of analytics rules. If any analytics rule in the list triggers, the given analytics rule doesn't trigger. | Optional |
|
anomalyThreshold | The period of time the model for the analytics rule remembers and trains on an observed data point. After this period, the model forgets the data point and the analytics rule can trigger on the data point again. | Mandatory |
|
checkScopeMaturity | Whether the rule should learn more about the entities defined in | Optional |
|
maturityThreshold | The duration of the training period for | Optional |
|
query | A query that retrieves the specific events that triggered the analytics rule. In many cases, The events retrieved using | Mandatory |
|
familyId | The analytics rule family to which the rule belongs. | Mandatory |
|
ruleGroupId | The analytics rule group to which the rule belongs. | Mandatory |
|