- Dashboards
- Navigation Overview
- View and Interact with an Open Dashboard
- View and Interact with an Open Visualization
- User Management
- Configure and Manage Dashboards
- Create a Dashboard
- Add a Visualization to a Dashboard
- Add a Text Tile
- Modify a Dashboard Layout
- Add Dashboard Filters
- Manage Automatic Refresh Rates
- Create a Scheduled Report
- Make a Dashboard Public
- Export and Import Dashboards
- Edit Dashboard Filters
- Edit Dashboard Details
- Duplicate a Dashboard
- Delete a Dashboard
- Configure and Manage Visualizations
- Create a Visualization Using the Basic Method
- Auto-Create a Visualization from a Natural Language Prompt
- Create a Visualization from a Search Query
- Add Visualizations from the Library to a Dashboard
- Modify a Visualization
- Configure Visualization Query Filters
- Include Context Filtering in Visualizations
- Make a Visualization Public
- Export and Import Visualizations
- Duplicate a Visualization
- Remove a Visualization from a Dashboard
- Delete Visualizations from the Library
- Configure and Manage Scheduled Reports
- Pre-Built Dashboards
- Advanced Analytics Dashboards
- AI/LLM Dashboards
- Case Manager Dashboards
- Compliance Dashboards
- Correlation Rules Dashboards
- Event Store Dashboards
- Access Grant and Revoke Activity
- Account Logout Summary
- Account Management Activity
- Application Security Event Summary
- Authenticated User Accounts on Hosts
- AWS CloudTrail Summary
- Data Loss Prevention Activity – Host-Based
- Data Loss Prevention Activity – User-Based
- Data Loss Prevention Activity Summary
- Default Account Access
- Default Credential Usage and Change Activity
- Denied Web Access Activity
- Disabled User Account Summary
- Discovered Attacks by Source and Destination
- Endpoint Detection and Response
- Failed Application Logon Activity
- Failed Audit Logs Summary
- Failed Host Login Attempt Counts by Users
- Failed VPN Login Attempts and Remote Session Timeouts
- Firewall Activity
- Firewall and Router Device Interfaces
- Insecure Authentication Attempts
- IOC Statistics
- Log Delay Insights
- Microsoft 365 Summary
- Microsoft Windows Overview
- Network Applications by Traffic Volume
- Policy Activity Summary
- Ports Usage Trend
- Privileged Access
- Privileged Access – User-Based
- Project Collateral
- Protocols by Network Traffic
- Remote Session Overview
- Security Alert Summary – Impacted Hosts
- Security Alert Summary – Origin Hosts
- Security Alert Summary – Users
- Successful Application Logon Activity
- Successful Database Login Activity
- Successful Physical Access
- Top Attackers
- User Account Creation Summary
- User Account Lockout Activity
- Vendor Authentication Activity
- Windows Audit Failure Summary by Hosts
- Windows Audit Failure Summary by Users
- Windows User Privilege Elevation
- Zscaler HTTP Dashboard
- Security Operations Center Management Dashboards
- Threat Center Dashboards
- Pre-Built Visualizations
- Agentic AI - Result
- Agentic AI - Violations
- Agentic AI by App ID
- Agentic AI Usage by Host
- Agentic AI Users - Blicked/Allowed
- Anomalies - Use Case & MITRE Coverage
- Anomalies by Rule Name
- Anomalies by Use Case
- Anomalies Count Over Time
- Anomaly Distribution by MITRE Tactic & Score
- Application Count
- Closed Incidents
- Correlation Rules by Severity
- Correlation Rules Triggered Over Time
- Detected Anomalies
- Host-Based DLP Alerts Count
- Incidents Created
- Incident Summary by Incident Type
- Number of Hosts with DLP Alerts
- SOC Incident Distribution
- Top 5 Host-Based DLP Alert Categories
- Top 5 Protocols in Host-Based DLP Alerts
- Top 10 Host-Based DLP Alert Types
- Top 10 Hosts with DLP Alerts
- Top Activities per Top 10 Applications
- Top Users per Top 10 Applications
- Trend of Application Security Events
Microsoft Windows Overview
The Microsoft Windows Overview dashboard provides a break down of the Microsoft Windows events in your organization.
Note
This dashboard can assist you in complying with the following regulatory requirements: HIPAA, ISO 27001, NIST, PCI, TSC SOC2.
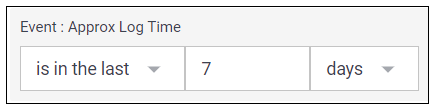
Time Range Filter
The Event : Approx Log Time filter sets the time range for the event data. The default setting is in the last 7 days. You can update this filter with a wide range of customizable settings.
To update the time range filter, click the arrow ( ) on the right, under the Edit button, to expand the filters panel. In the Event : Approx Log Time filter, select an operator from the first drop down menu and then enter or select values in the subsequent fields, depending on the operator you selected. To save your filter changes, click Apply on the right side of the filter panel. The updated filter is applied to the visualization.
) on the right, under the Edit button, to expand the filters panel. In the Event : Approx Log Time filter, select an operator from the first drop down menu and then enter or select values in the subsequent fields, depending on the operator you selected. To save your filter changes, click Apply on the right side of the filter panel. The updated filter is applied to the visualization.
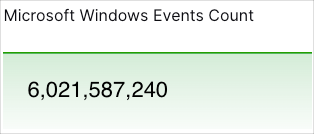
Microsoft Windows Events Count
This single value bar chart displays the number of Microsoft Windows events that have been triggered in your organization over the selected time range.
Number of Devices Logging into Microsoft Windows
This single value bar chart displays the number of different devices that have logged into Microsoft Windows over the selected time range.
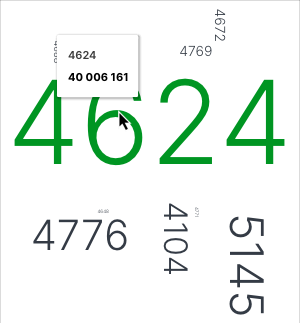
Number of Events per Event Code
This word cloud provides a visualization of the event codes have been triggered most frequently. Larger text indicates a greater event frequency. Hover your pointer over the codes to view their count values. To view the underlying events of a value, click the event code, and then click Show Results in Search.
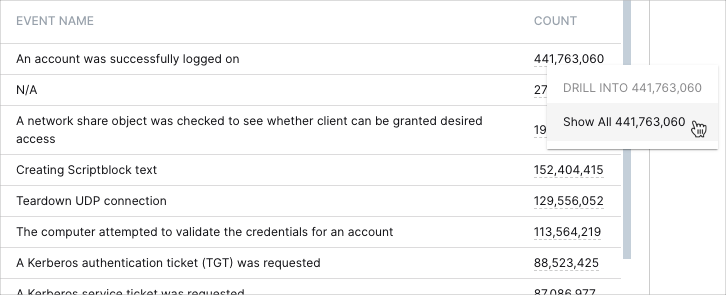
Microsoft Windows Event Information
This table lists the event codes and their event names along with the number of times they have been triggered.
To view all the events, you may need to use the scroll bar on the right. To view the underlying events of a count value, click the value, and then click Show Results in Search.
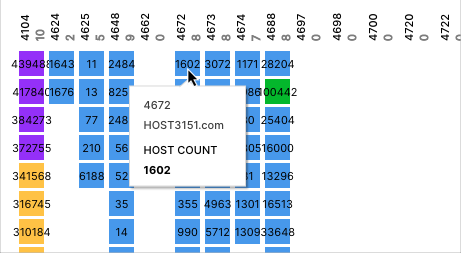
Microsoft Windows Events Coverage Map
This coverage map lists the different Windows event codes and uses colored squares to represent the hosts in which they're being triggered. The numbers on the squares indicate the number of times that the event has been triggered, and the different colors represent number ranges that are given in the legend. Hover your pointer over the squares to display the host names. To view the underlying events of a value, click the square, and then click Show Results in Search.
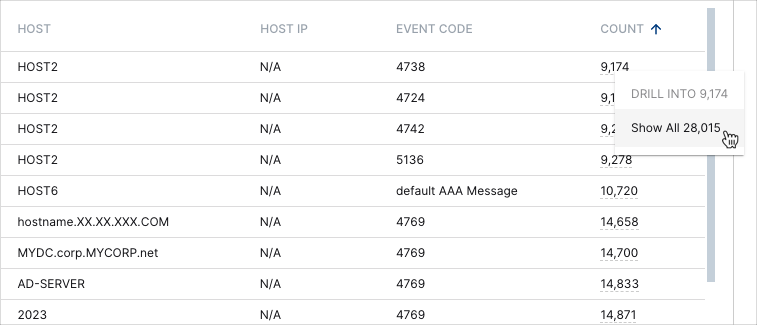
Microsoft Windows Events Per Host
This table provides details on the different hosts in your deployment and the Windows events that have been triggered in them. Click the heading of the column that you want to sort the data by. Click the arrow icon to change between ascending  and descending
and descending  orders. To view all the rows on the table, you may need to use the scroll bar on the right.
orders. To view all the rows on the table, you may need to use the scroll bar on the right.
To view the underlying events of a value, click the value, and then click Show Results in Search.