- 2026 Release Notes
- May 2026
- April 2026
- March 2026
- February 2026
- January 2026
- 2025 Release Notes
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- July 2025
- June 2025
- May 2025
- April 2025
- March 2025
- February 2025
- January 2025
- Known Issues
February 2026
The New-Scale Security Operations Platform includes the following addressed features and new features for February 2026.
Automation Management
Feature | Description |
|---|---|
Automation Agent Name Format Enhancement | You now precisely identify automation agents with a new automation agent name format. The automation agent name now appears with your Exabeam instance name appended to it in the format <automationagent>-<instance>. For example, if the automation agent emea was created under the acme.exabeam.cloud instance, the automation agent name appears as emea-acme. 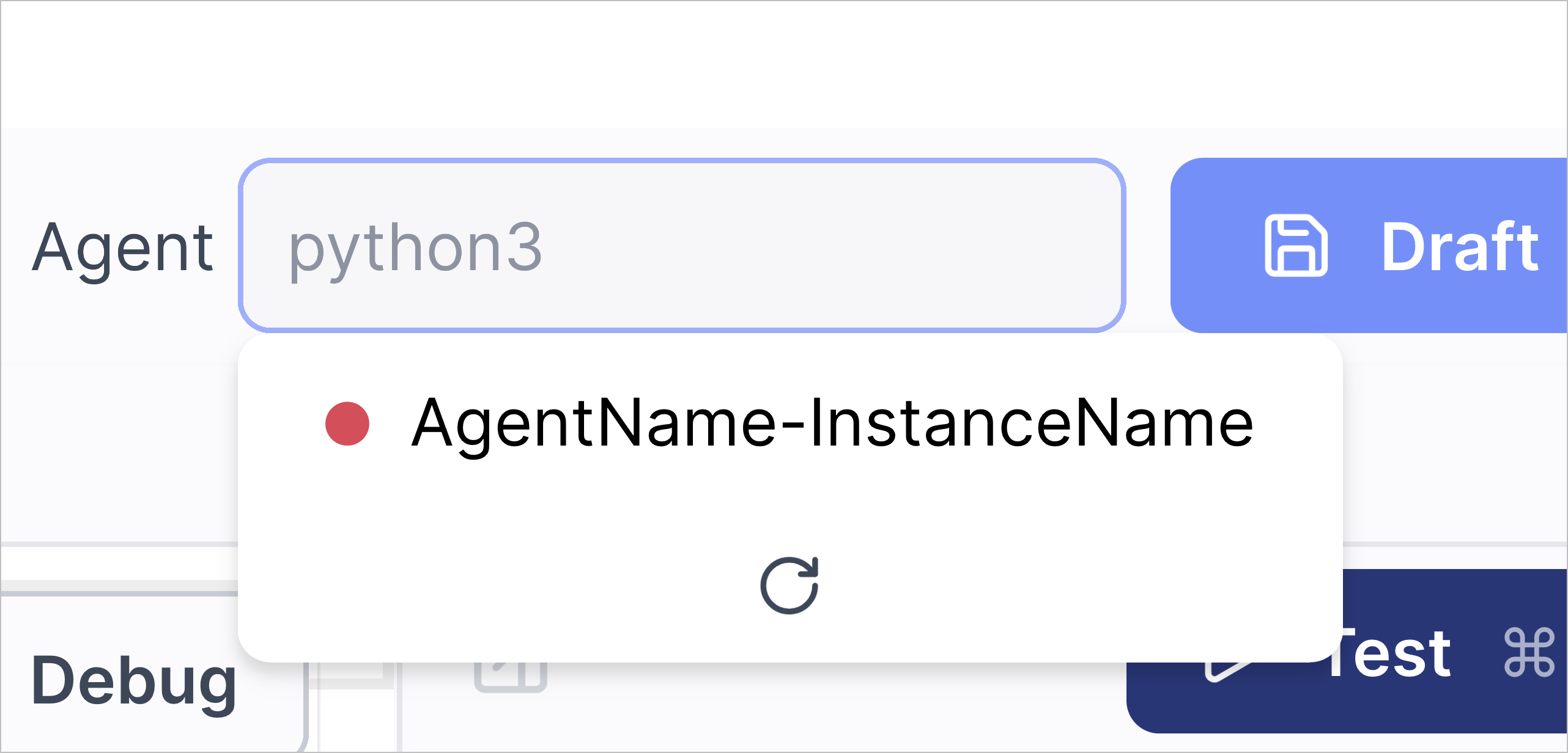 To support this new format:
|
Advanced Playbook Variable Reliability Enhancement | To more reliably create advanced playbooks, only service instance parameters of the string data type now appear as variables in advanced playbooks. |
Pre-built Set Default assignee and queue Playbook Enhancement | To ensure the pre-built Set Default assignee and queue playbook is compatible with various Threat Center queue configurations, it now assigns new cases with a risk score above 90 to the Unassigned queue. |
Cloud Collectors
Feature | Description |
|---|---|
Mimecast Incydr Cloud Collector | The Mimecast Incydr cloud collector is now available as part of Cloud Collectors to facilitate ingestion of events from the File events data source. |
Early Access Collectors | |
S2W Threat Intelligence Cloud Collector | The S2W Threat Intelligence Cloud Collector is now available as part of Cloud Collectors Early Access program, to facilitate ingestion of threat intelligence data, such as threat detections, brand or digital abuse, and blockchain data. The early access program offers you an opportunity to gain access to the latest cloud collectors before their official release. To participate, see Sign Up for the Early Access Program. |
Context Management
Feature | Description |
|---|---|
Option to Add Rows of Data to Filtered Tables is Removed | Filtered context tables can contain data from multiple parent tables. When the data in the parent tables are updated, the filtered table is automatically updated and any data added directly to the filtered table, either manually or via CSV, is overwritten. For this reason, the option to add rows of data directly to a filtered context table has been removed. Instead, add the desired rows of data to one of the parent context tables. For more information, see View and Interact with a Custom or Filtered Context Table in the Context Management Guide. |
Correlation Rules
Feature | Description |
|---|---|
Correlation Rule Stopped Status Tooltip Enhancement | To better understand why a correlation rule is stopped, when you hover over the Stopped status, you can now view an enhanced tooltip that explains that a correlation rule may be stopped because of incorrect query syntax or a reference to an empty context table. The tooltip now states: Please check the rule's query for any context tables which no longer exist or such thing as custom or metadata fields that are no longer relevant. 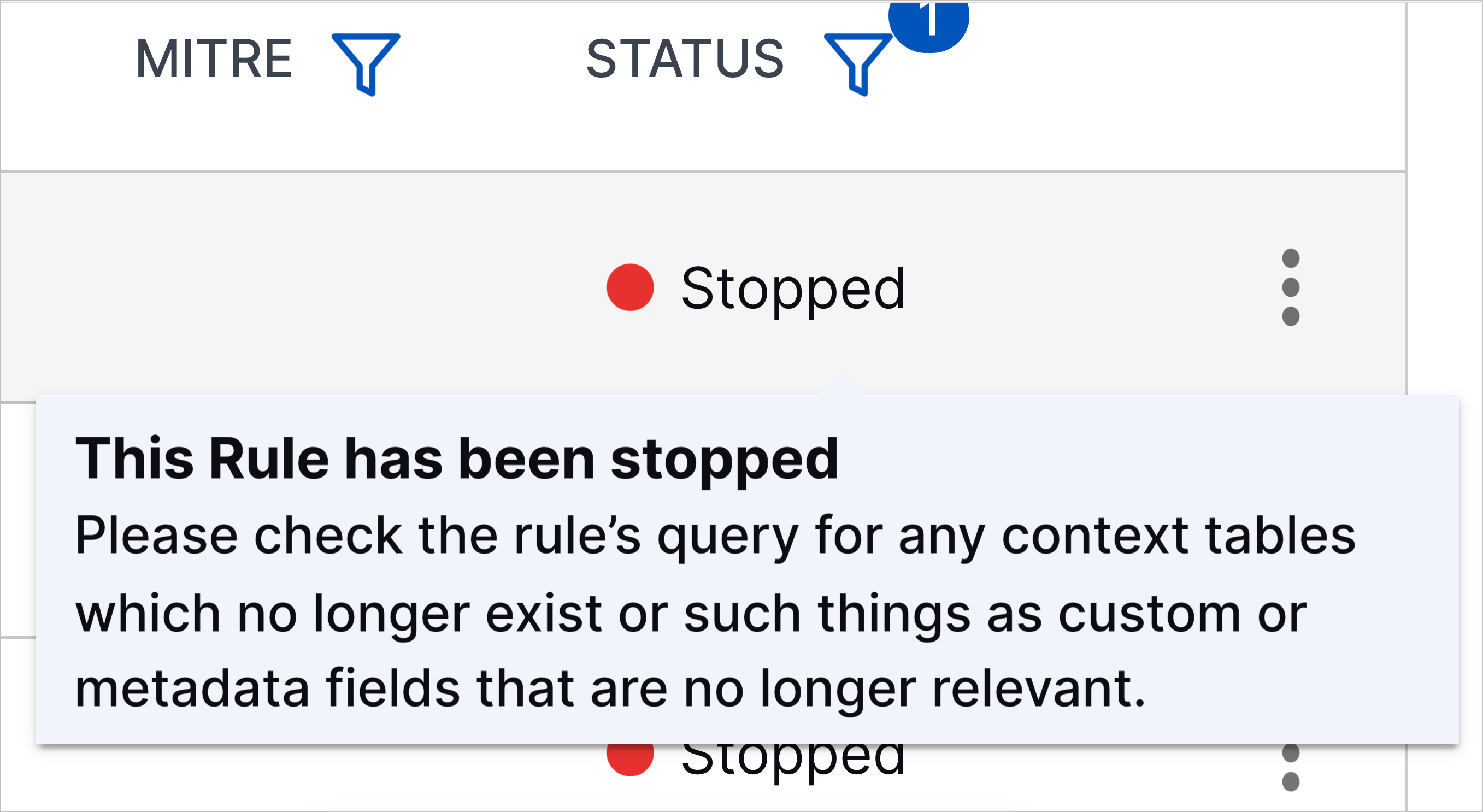 |
New Correlation Rule Templates | You can now better detect unauthorized cloud account access, email-based attacks, and remote code execution with new correlation rule templates:
|
Log Stream
Feature | Description |
|---|---|
Enhanced Host to IP Enrichment | New-Scale Host to IP enrichment has been enhanced two new opportunities for managing the host to IP enrichment mapping process. Previously available only as early access functionality, these opportunities are now available to all user as described below:
For more information about this type of enrichment, see Host to IP Enrichment in the Log Stream Guide. |
Increased Visibility for Enriched Fields | The Log Stream Enrichment tab has been enhanced to surface the fields that have been enriched by each enrichment rule. A new Enriched Fields column has been added to the table of enrichment rules to show which field is being enriched by each rule. If multiple fields are being enriched, the fields are displayed in a comma-separated list. This new column makes it possible to see the enriched fields without the need to drill into the rule definition details. You can also filter the new column to change the table so it displays only those rules that enrich specific fields. For more information about this type of enrichment, see Navigating the Enrichments Tab in the Log Stream Guide. |
Reserved Fields Restricted from Enrichment Mapping | Guardrails have been added to the enrichment rule definition process to ensure that certain reserved fields are restricted from use for enrichment mapping. You also cannot import enrichment rules that include reserved fields. For a list of these restricted fields, see Reserved Fields. |
No Disabling of Slow Performing Parsers | In Advanced Analytics, when a slow performing parser was detected, the assumption was that a problem with the parser definition might be causing the slow performance and the parser was automatically disabled. However, in Log Stream, a slow performing parser is less likely caused by a parser definition issue than by a possible service issue. In such cases, automatically disabling the parser is unnecessary and can cause disruptions in data parsing. For these reasons, the practice of automatically disabling slow performing parsers has been discontinued. However, you can still choose to manually disable such parsers. For information about disabling a parser, see Enable or Disable Parsers in the Log Stream Guide. |
Custom Default Parser Disablement Complete | As of February, 2026, the process of discontinuing the Custom Default parser category has been completed. This category has been removed in favor of a simpler, more consistent approach to handling default parsers that have been customized. For more information, see Parser Types in the Log Stream Guide. |
Clarification of Automatic Content Package Updates | A warning has been added to clarify the benefits and risks that should be considered before activating Auto-install updates on the Parser Updates tab in Log Stream. The bottom line is that content package updates must be installed on a regular cadence, whether you opt to auto-install them or manually install them. For more information, see Parser Updates in the Log Stream Guide. |
New-Scale Platform
Feature | Description |
|---|---|
Success Center | To quickly access information about your account team, announcements, links to training and more, you now have a customized Success Center directly in the New-Scale Security Operations Platform. To access your Success Center, click on the new ribbon icon in the upper right-hand corner. 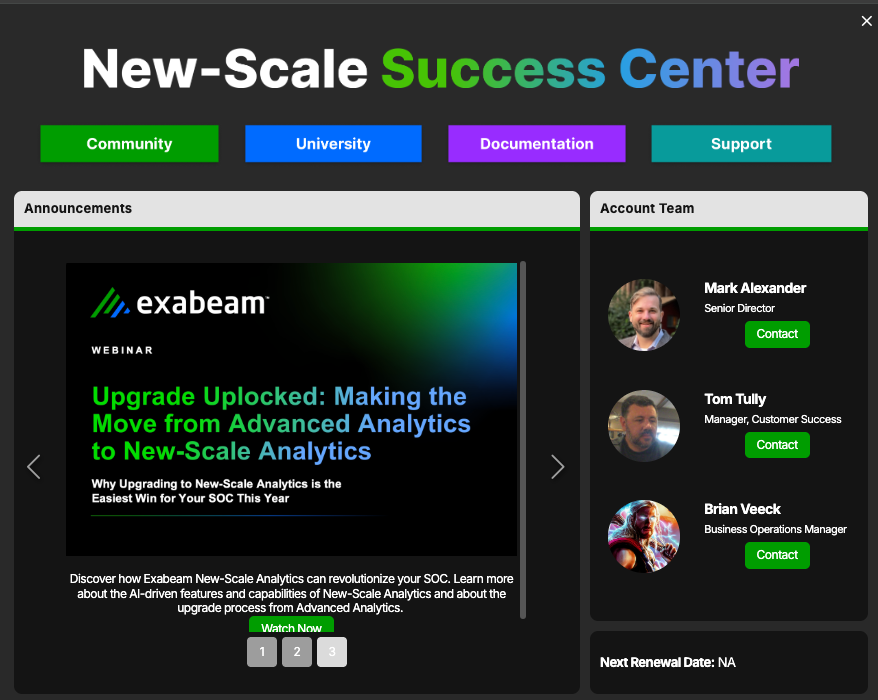 |
Outcomes Navigator
Feature | Description |
|---|---|
Agentic AI Security Use Case Support | You can now use Outcomes Navigator to assess how well your environment protects against agentic AI threats. Agentic AI Security is a new use case under the Compromised Insiders use case category. Like other use cases in Outcomes Navigator, you can assess the current state of your configuration, see where there are gaps, and view recommendations to improve your protection against agentic AI threats. 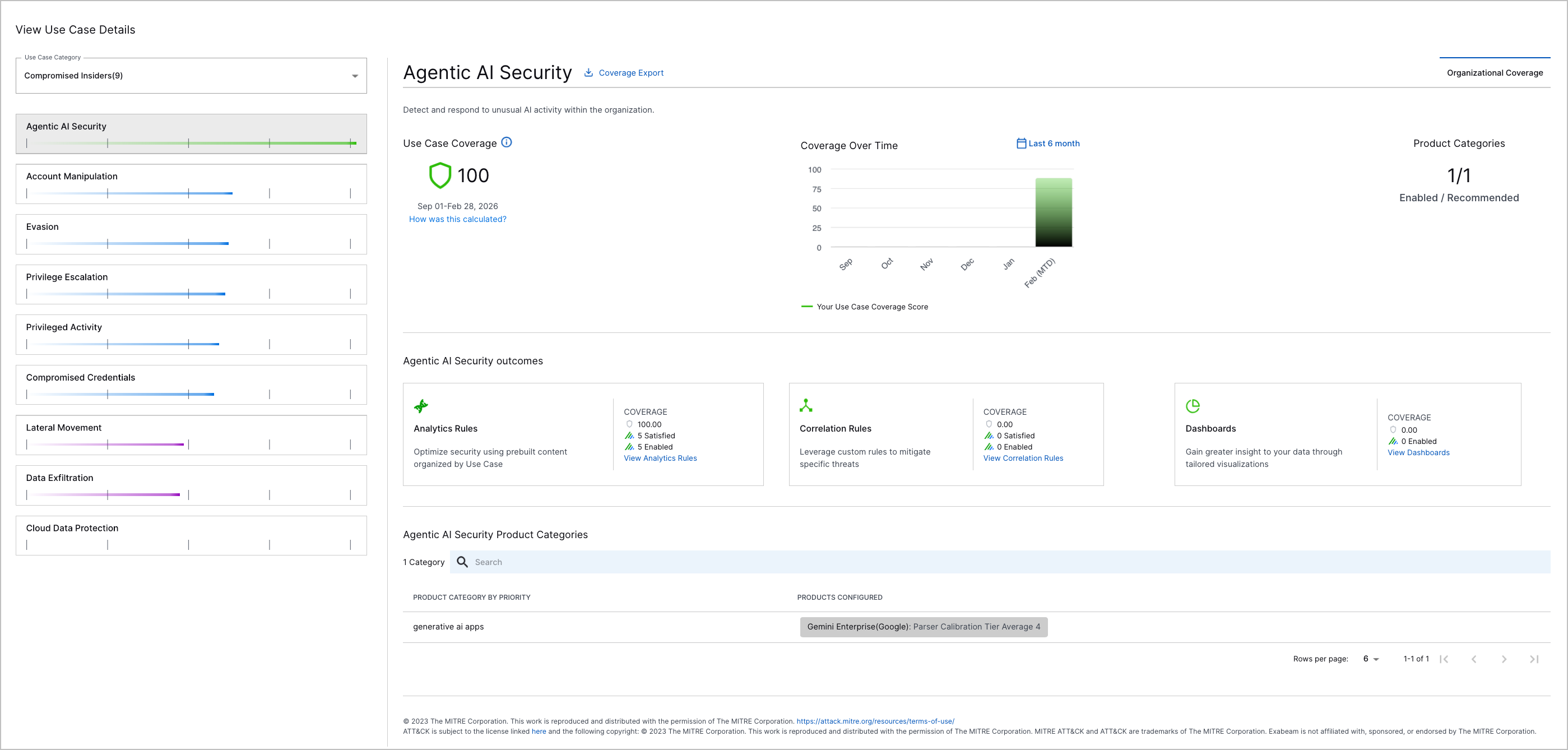 |
Search
Feature | Description | |
|---|---|---|
Enhancement to the Timeline View | The Timeline view of search results has been enhanced to provide a more complete investigational experience. Previously, when a search query returned a detection, but the associated source event did not meet the query criteria, the detection was displayed alone with an For more information, see Timeline View of Search Results in the Search Guide. | |
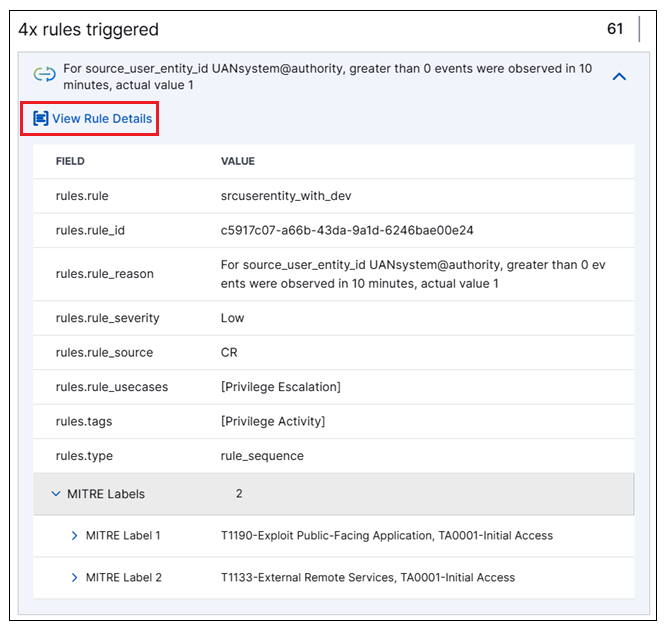
Access to View Rule Definitions | A new capability to view rule definitions without leaving the Search application is now available. When you open a Detection tab in the Details panel to view information about a specific detection, the rules that triggered the detection are listed. You can expand the rules to view all of the supporting fields. If the rule you expand is a primary rule (not a context rule), a new View Rule Details link is now available.
Click the new link to open a Rule Details panel that provides immediate, in-context access to rule information, including the configured rule definition. This panel makes the rule definition and other rule information accessible for examination without navigating away from your search results. For more information, see Detection Details in the Search Guide. |
Threat Detection Management
Feature | Description |
|---|---|
Training Period for Select Analytics Rules | To prevent profiledFeature, numericCountProfiledFeature, numericDistinctCountProfiledFeature, and numericSumProfiledFeature analytics rules from over-triggering on first-time observations and to ensure they establish a good baseline, you can now configure them to train on live data for a specified period before they begin triggering. To configure a training period, add the 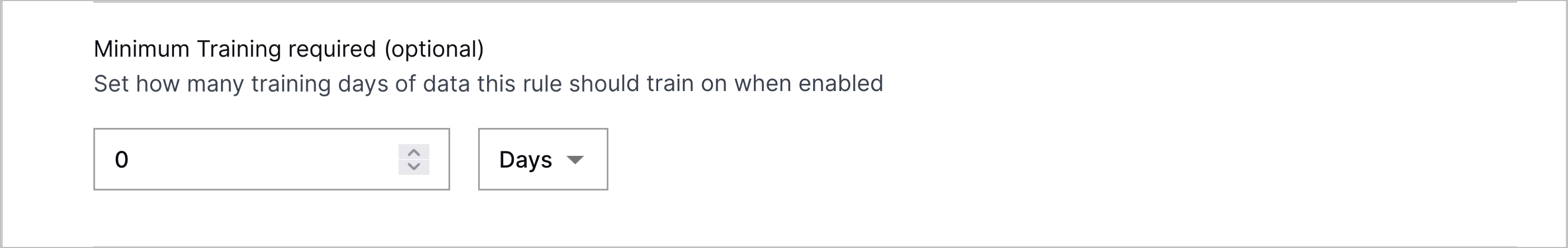 Disabling the analytics rule resets its training. When re-enabled, the analytics rule must complete its training period before it can begin triggering again. Editing an enabled analytics rule doesn't reset its training. When an analytics rule is training, its status is set to Training and it can't trigger. After the rule is finished training, its status is automatically changed to Enabled. |
Expanded CIM Fields for Analytics Rule Builder Applicable Events | To more precisely define which events an analytics rule evaluates using the analytics rule builder, you can now select from all CIM 2.0 fields when defining applicable events. 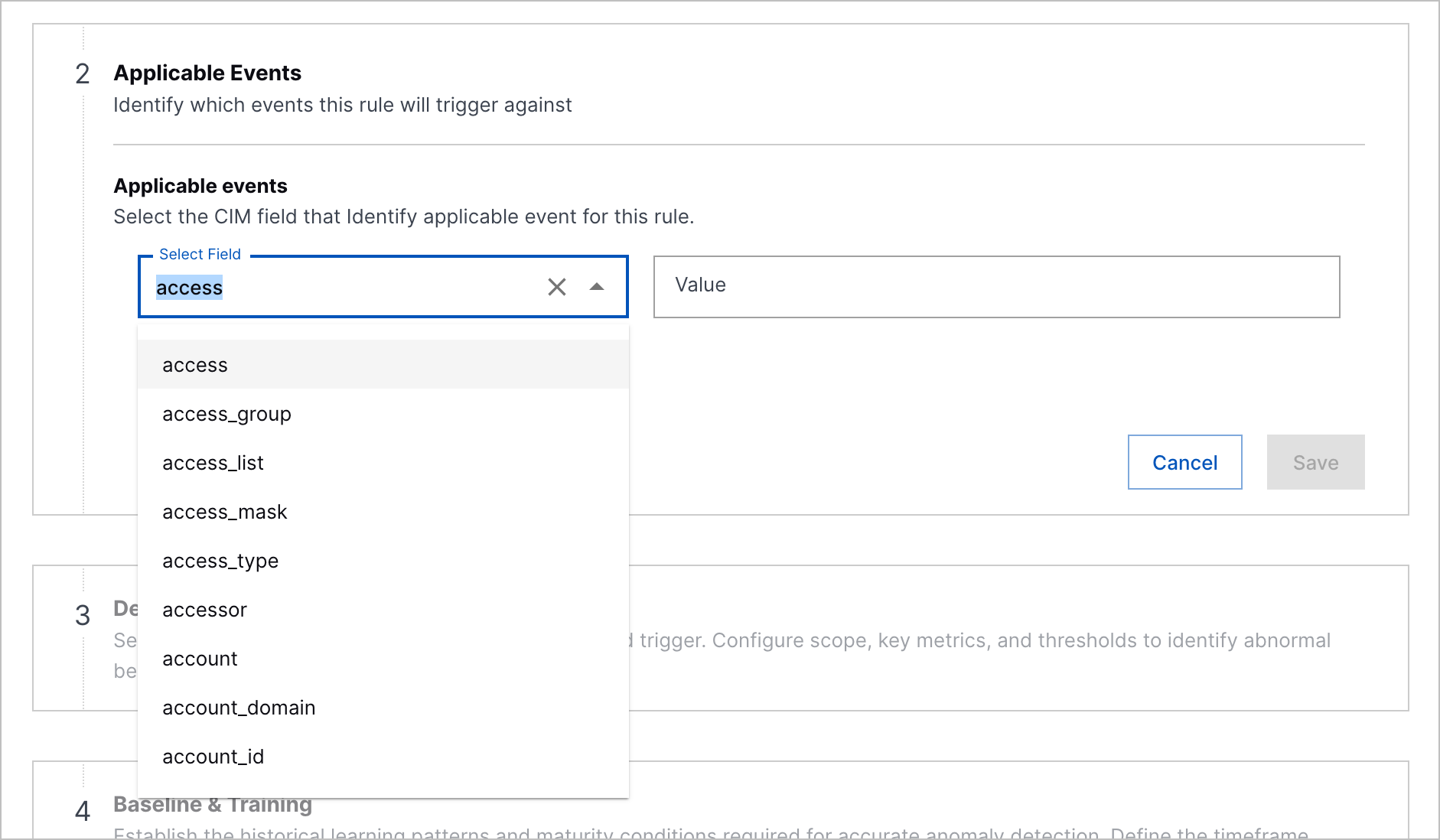 |
Expanded | You can now set higher trigger thresholds for numericCountProfiledFeature, numericDistinctCountProfiledFeature, and numericSumProfiledFeature analytics rules using the A valid value for the |
featureValue Validation for numericSumProfiledFeature Analytics Rules | To improve the reliability of numericSumProfiledFeature analytics rules, you can now only use event fields that return numeric values for the |
Suppress Length Toggle | If you don't want to suppress an analytics rule from triggering repeatedly on a specified field, you can now toggle suppression off under Suppress Length.  |
Correlation Rule Stopped Status Tooltip Enhancement | To better understand why a correlation rule is stopped, when you hover over the Stopped status, you can now view an enhanced tooltip that explains that a correlation rule may be stopped because of incorrect query syntax or a reference to an empty context table. The tooltip now states: Please check the rule's query for any context tables which no longer exist or such thing as custom or metadata fields that are no longer relevant. 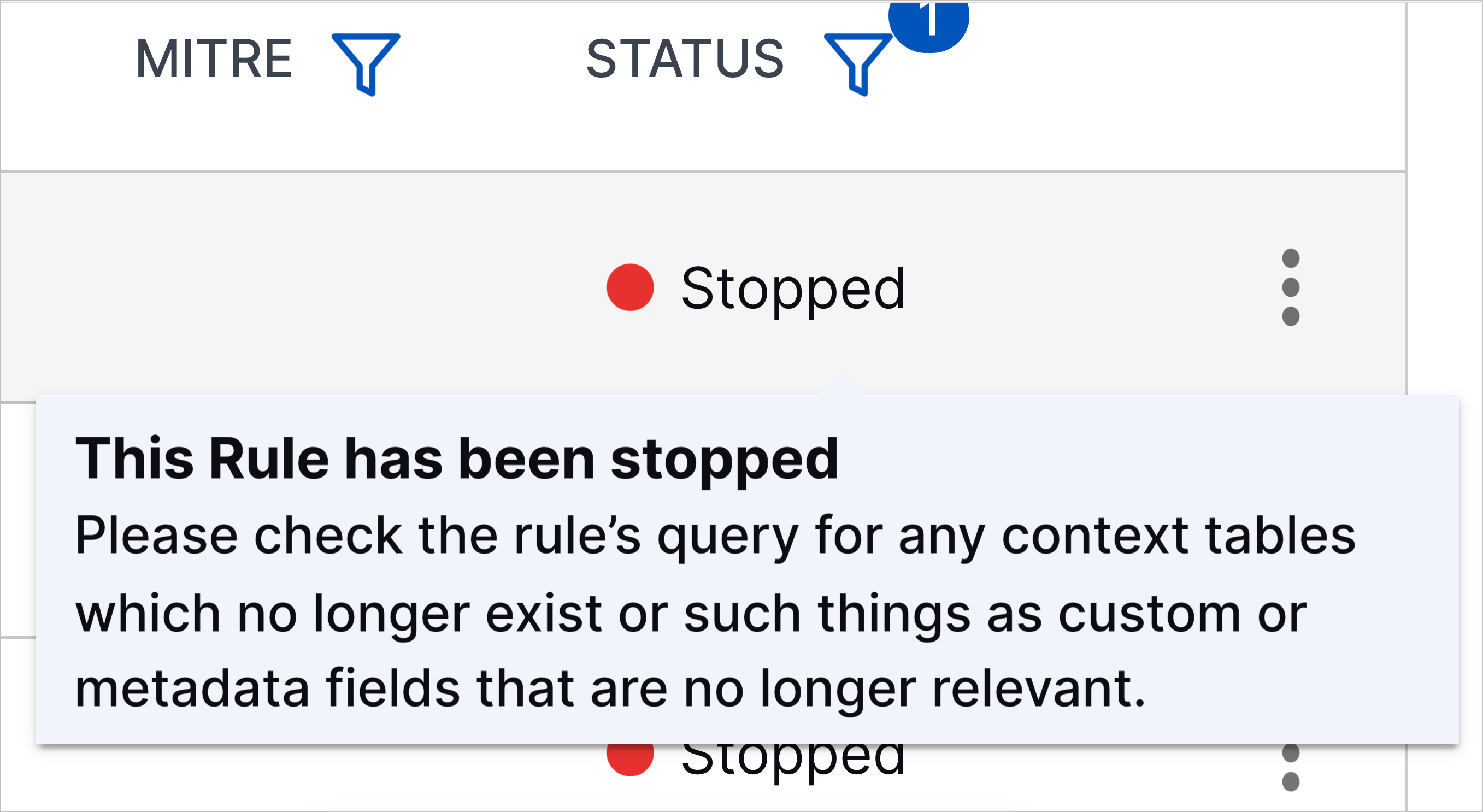 |
New Correlation Rule Templates | You can now better detect unauthorized cloud account access, email-based attacks, and remote code execution with new correlation rule templates:
|
New and Updated Pre-Built Analytics Rules | You can now better detect credential dumping, privilege escalation, persistence, data exfiltration, lateral movement, RDP session hijacking, Kerberos-based attacks, malicious code execution, and AI misuse with new and updated analytics rules. New pre-built analytics rules include:
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which
Pre-built analytics rules for which actOnCondition was updated include:
Removed obsolete pre-built analytics include:
|