- Get Started with Threat Center
- Threat Center
- Threat Center Permissions
- Threat Center Alerts: Read
- Threat Center Alerts: Read, Write, and Delete
- Threat Center Cases: Read
- Threat Center Cases: Read, Write, and Delete
- Threat Center Detection Grouping Rules: Read
- Threat Center Detection Grouping Rules: Read, Write, and Delete
- Threat Center Watchlist: Read
- Threat Center Watchlist: Read, Write, and Delete
- Threat Center Cases
- Threat Center Alerts
- Threat Center Detections
- Threat Center Risk Score
- Configure Threat Center
- Monitor Entities of Interest in Threat Center
- Work on Cases
- Work on Alerts
- Edit and Collaborate in Threat Center
- Use Automation Tools in Threat Center
- Find Cases and Alerts
- View Case and Alert Metrics
- Get Notified About Threat Center
- Threat Center APIs
Create a Detection Grouping Rule
Create a detection grouping rule to group related detections according to criteria you specify.
You can create up to 20 detection grouping rules.
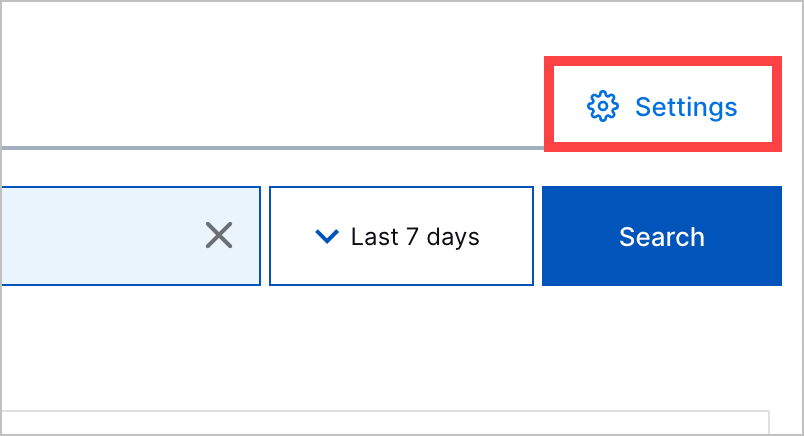
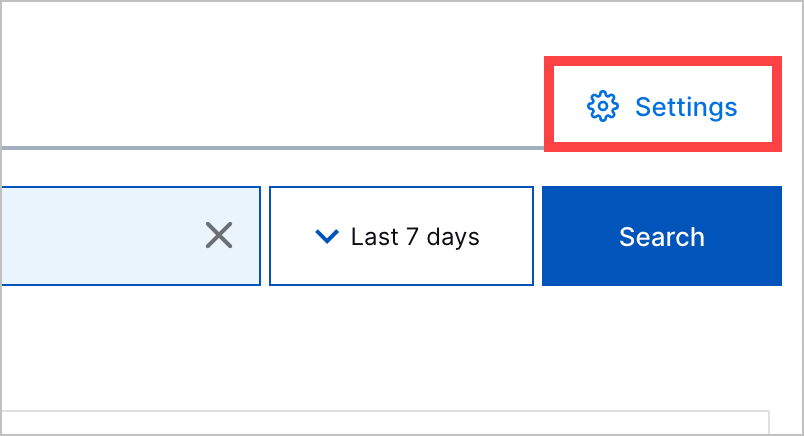
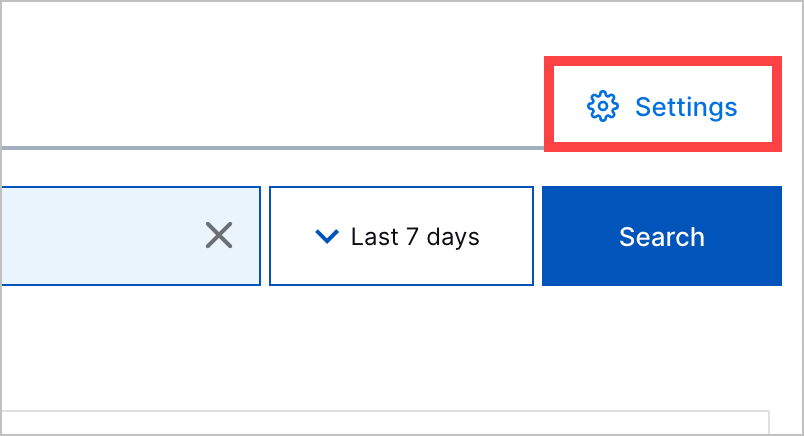
In Threat Center, click Settings, then navigate to the Detection grouping rules tab.
Click + New Rule.
In New Detection Name, enter the rule name. You can't rename the rule after you save it.
Under Trigger, select Select trigger, then select is created.
Under Condition, define the conditions a detection must satisfy for the rule to apply to the detection. If you're grouping a detection by a certain field, one of the conditions must be that the field exists to ensure the detection contains the field and preserve the grouping logic; for example, if you're grouping detections by field Src Ip, one of the conditions must be Src Ip exists.
Click Select object, then select a field from the list.
Click Select condition, then select an operator from the list. Depending on the operator you select, you may need to enter a value.
(Optional) To add additional conditions, click
 . All conditions must be satisfied for the rule to apply to the detection.
. All conditions must be satisfied for the rule to apply to the detection.
Under Action, define by which fields a detection is grouped. Click + Field, then select a field from the list. If not already defined, Threat Center adds the condition <field> exists. To group the detection by an additional field, click
 .
.If you're grouping detections by detection ID, the only additional field by which you can group detections is rule name.
Click Save.
Create Standalone Cases from Correlation Rules Using a Detection Grouping Rule
To identify Threat Center cases created as the outcome of a correlation rule, create a detection grouping rule that groups a correlation rule detection into a standalone case.
There are two approaches to grouping correlation rule detections into standalone cases. You can:
For a standalone case to be created, the detection grouping rule must be first in the list of detection grouping rules.
Group Correlation Rule Detections by Group By Field
Group detections from the same correlation rule and group by field into a single case.
In Threat Center, click Settings, then navigate to the Detection grouping rules tab.
Click + New Rule.
In New Detection Name, enter the rule name. You can't rename the rule after you save it.
Under Trigger, select Select trigger, then select is created.
Under Condition, you define the conditions a detection must satisfy for the rule to apply to the detection. All conditions must be satisfied for the rule to apply to the detection. To define multiple conditions, click
 .
.To create standalone cases from correlation rules, define the following conditions:
Rule Source is equals to Correlation Rule:
Click Select object, then select Rule Source.
Click Select condition, then select is equals to.
Click Enter value, then enter
Correlation Rule.
Rule Name exists:
Click Select object, then select Rule Name.
Click Select condition, then select exists.
GroupBy field exists:
Click Select object, then select GroupBy field.
Click Select condition, then select exists.
Create Case is equals to true:
Click Select object, then select Create Case.
Click Select condition, then select is equals to.
Click Enter value, then enter
true.
Under Action, you define the fields by which a detection is grouped. To define multiple actions, click
 .
.Define actions that group detections by rule name and group by field:
To group detections by rule name, click + Field, then select Rule Name.
To group detections by group by field, click + Field, then select GroupBy field.
Click Save. Ensure that the detection grouping rule is ordered first in the list.
Group Correlation Rule Detections by Correlation Rule Detection ID
Create a unique case for each individual correlation rule detection.
In Threat Center, click Settings, then navigate to the Detection grouping rules tab.
Click + New Rule.
In New Detection Name, enter the rule name. You can't rename the rule after you save it.
Under Trigger, select Select trigger, then select is created.
Under Condition, you define the conditions a detection must satisfy for the rule to apply to the detection. All conditions must be satisfied for the rule to apply to the detection. To define multiple conditions, click
 .
.To create standalone cases from correlation rules, define the following conditions:
Rule Source is equals to Correlation Rule:
Click Select object, then select Rule Source.
Click Select condition, then select is equals to.
Click Enter value, then enter
Correlation Rule.
Rule Name exists:
Click Select object, then select Rule Name.
Click Select condition, then select exists.
Detection Id exists:
Click Select object, then select Detection Id.
Click Select condition, then select exists.
Create Case is equals to true:
Click Select object, then select Create Case.
Click Select condition, then select is equals to.
Click Enter value, then enter
true.
Under Action, you define the fields by which a detection is grouped. To define multiple actions, click
 .
.To create a unique case for each individual detection, define actions that group detections by rule name and detection ID:
To group detections by rule name, click + Field, then select Rule Name.
To group detections by detection ID, click + Field, then select Detection Id.
Click Save. Ensure that the detection grouping rule is ordered first in the list.
