- Get Started with Threat Center
- Threat Center
- Threat Center Permissions
- Threat Center Alerts: Read
- Threat Center Alerts: Read, Write, and Delete
- Threat Center Cases: Read
- Threat Center Cases: Read, Write, and Delete
- Threat Center Detection Grouping Rules: Read
- Threat Center Detection Grouping Rules: Read, Write, and Delete
- Threat Center Watchlist: Read
- Threat Center Watchlist: Read, Write, and Delete
- Threat Center Cases
- Threat Center Alerts
- Threat Center Detections
- Threat Center Risk Score
- Configure Threat Center
- Monitor Entities of Interest in Threat Center
- Work on Cases
- Work on Alerts
- Edit and Collaborate in Threat Center
- Use Automation Tools in Threat Center
- Find Cases and Alerts
- View Case and Alert Metrics
- Get Notified About Threat Center
- Threat Center APIs
Manually Send Case or Alert Information to Webhooks
Manually send case or alert information directly from the case or alert to third-party systems using webhooks.
The webhook message contains case or alert attributes in a key-value JSON format. Case or alert attributes sent include:
last_update_time– The date and time the case or alert was last updatedcase_idoralert_id– The case or alert UUIDcase_number– The unique case ID assigned to the casealert_name– The alert namethreat_summary– A summary of the case or alert, including the number of related detections, triggered rules, MITRE ATT&CK® tactics and techniques, users, endpoints; the case or alert risk score; and the attribute by which related detections are groupedtags– Associated tagsmitres– Associated ATT&CK tactics and techniquesuse_cases– Associated Exabeam use casesusers– Associated usersendpoints– Associated endpointspriority– Case or alert severitystage– Case stagequeue– The queue assigned to respond to the caseassignee– The assignee assigned to respond to the casedetections– Details for every related detection, including the detection type, associated Exabeam use case, associated triggered rules, approx_log_time, description, detection ID, associated source and destination users, associated source and destination IP addresses, and associated source and destination host namescase_closed_reason– If the case is closed, the selected pre-defined case closed reasoncase_close_supporting_reason– If the case is closed, the comment added to the pre-defined case closed reasonalert_created_time– The date and time the alert was createdcase_created_time– The date and time the case was createdcase_closed_time– The date and time the case stage was changed to Closed
To automatically send case or alert information to webhooks under specific situations and conditions you specify, create an Automation Management playbook where an action is Send all threat details via webhook.
You must have the Manage webhooks: Read, Write and Delete permission.
Ensure that you've added the webhook in New-Scale Security Operations Platform settings.
In a case or alert, click Actions, then select Send to webhook.
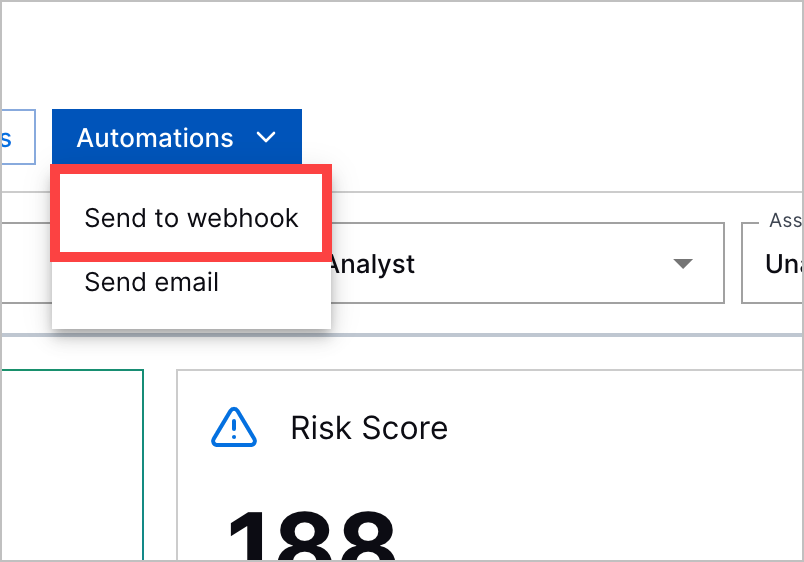
Select up to three webhooks to which you'll send case or alert information.
To add additional webhooks, click Add a new webhook in settings. You're redirected to New-Scale Security Operations Platform settings. After you add the webhook, return to sending a webook in Threat Center. To retrieve the latest list of webhooks, click
 .
.Click Send. This action is recorded in the case or alert history.
