- Get Started with Threat Center
- Group Detections
- Work on Cases
- Triage Alerts in Threat Center
- Edit and Collaborate in Threat Center
- Find Cases or Alerts
- Build a Search in Threat Center
- Enter a Search Using Exabeam Query Language in Threat Center
- Enter a Search Using Natural Language in Threat Center
- Run a Recent Search in Threat Center
- Create a New Saved Search in Threat Center
- Run a Saved Search in Threat Center
- Edit a Saved Search in Threat Center
- Delete a Saved Search in Threat Center
- Sort Cases or Alerts
- View Case and Alert Metrics
- Get Notified About Threat Center
Search for alerts of interest. To search for alerts that have likely not been triaged, search for alerts without an associated case. If you don't have the read permission for Threat Center cases, you only see alerts without an associated case.
By default, alerts are sorted by risk score, from highest to lowest. You can also manually sort alerts by risk score or age.
Get an overview of alerts of interest:
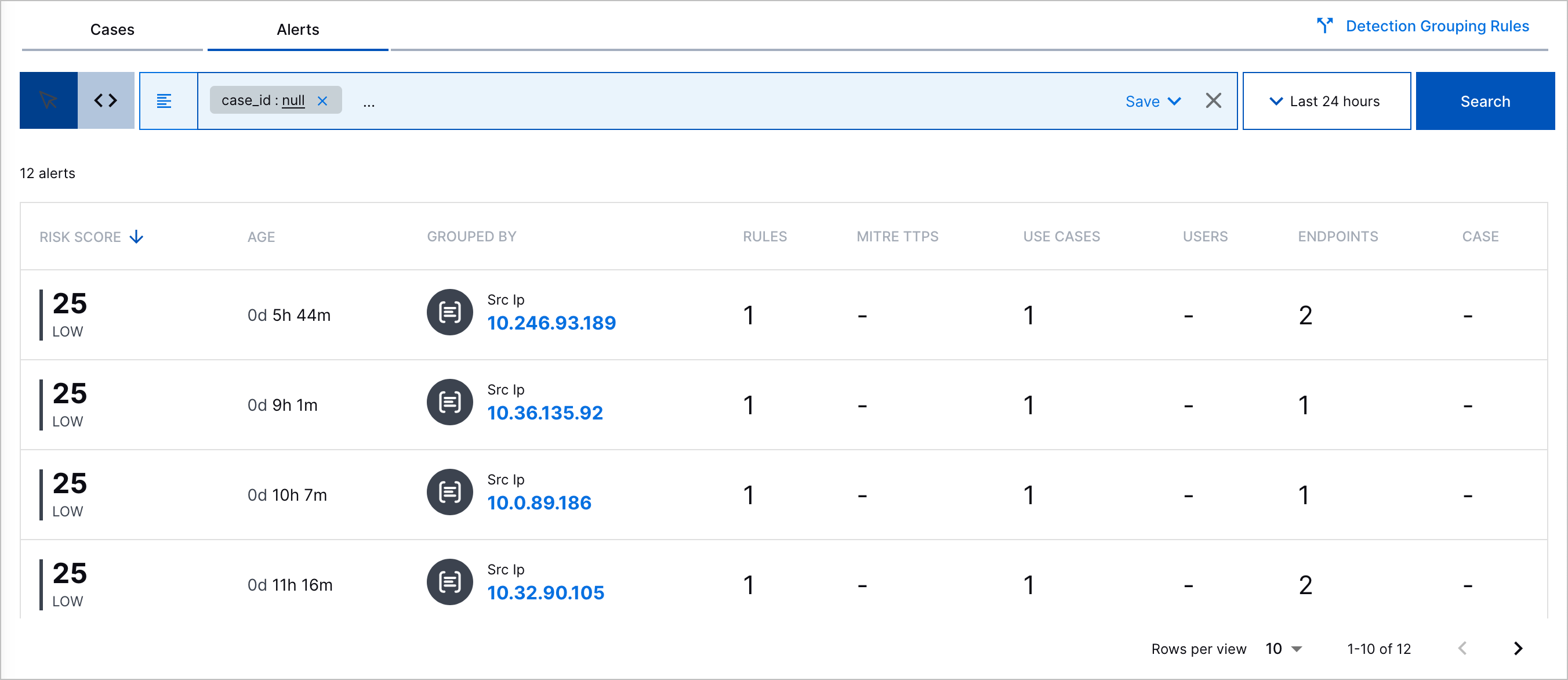
Risk Score – The alert risk score and associated priority: critical, high, medium, or low.
Age – The time elapsed since the alert was created.
Grouped By – The attribute by which detections are grouped.
Rules – The number of triggered correlation or Advanced Analytics rules associated with related detections.
MITRE TTPs – The number of MITRE ATT&CK® tactics and techniques the alert best describes.[6]
Use Cases – The number of Exabeam use cases the alert best describes.
Users – The number of users associated with related detections.
Endpoints – The number of source and destination hosts associated with related detections.
Case – Whether the alert is associated with a case. To view this column, you must have Threat Center Cases: Read or Threat Center Cases: Read, Write, and Delete permissions.
 indicates the alert is associated with a case; a dash indicates the alert isn't associated with a case.
indicates the alert is associated with a case; a dash indicates the alert isn't associated with a case.
To view more information, select the alert.
If the alert has an associated case, you're redirected to the case so you can respond to it.
In the Overview tab, get an overview of the alert:
Copilot Threat Summary – An AI-generated summary of the alert and recommended next steps. This summary is updated every time detections are added to the alert.
Risk Score – The case risk score and associated priority.
User Description – The alert description.
Grouped By – The attribute by which detections are grouped.
Timeframe – Important markers of time associated with the alert, including:
First Detection – The date and time the first detection was added to the alert.
Duration – The days, hours, and minutes elapsed between when the first and last detection was added to the alert.
Users – Users associated with related detections.
Devices – The source and destination hosts associated with related detections.
Rules Triggered – The triggered rules from which associated detections are created and the number of times they created associated detections.
MITRE TTP(s) – The ATT&CK tactics and techniques that best describe the alert.
Use Cases – The Exabeam use cases that best describe the case.
Under the Threat Timeline tab, understand the historical context around the alert. View a timeline of grouped detections, up to 100 associated parsed events, and key response moments, including when the alert was created.
To continue your investigation and view the event in Search, click Open in Search.
To view all detection details, including the assigned risk score, ATT&CK tactics and techniques, Exabeam use cases, tags, and event fields associated with the detection, click View All.
To view all parsed event fields, click View All Fields.
For Advanced Analytics detections, to review all events for the user or asset in the Advanced Analytics Smart Timeline™, click View Timeline in Advanced Analytics.
For Correlation Rules detections, to review more information about the correlation rule that created the detection, click Rule Definition:
Name – The correlation rule name.
Author – Who created the correlation rule.
Severity – The rule severity: None, Low, Medium, High or Critical.
Use Case – The Exabeam use case most relevant to the rule.
MITRE Properties – The ATT&CK techniques most relevant to the rule.
Tags – Tags associated with the rule.
Repeating Triggers – The field values by which the rule is suppressed if the rule is over-triggered.
As you triage an alert:
Update the alert attributes, like name, description, priority, related ATT&CK tactic and techniques, related Exabeam use cases, or tags, with the latest information.
Expedite your alert triage and get answers to any question about the alert or related entities using the Copilot Analyst Assistant. To navigate to the Copilot Analyst Assistant, click Open Analyst Assistant:
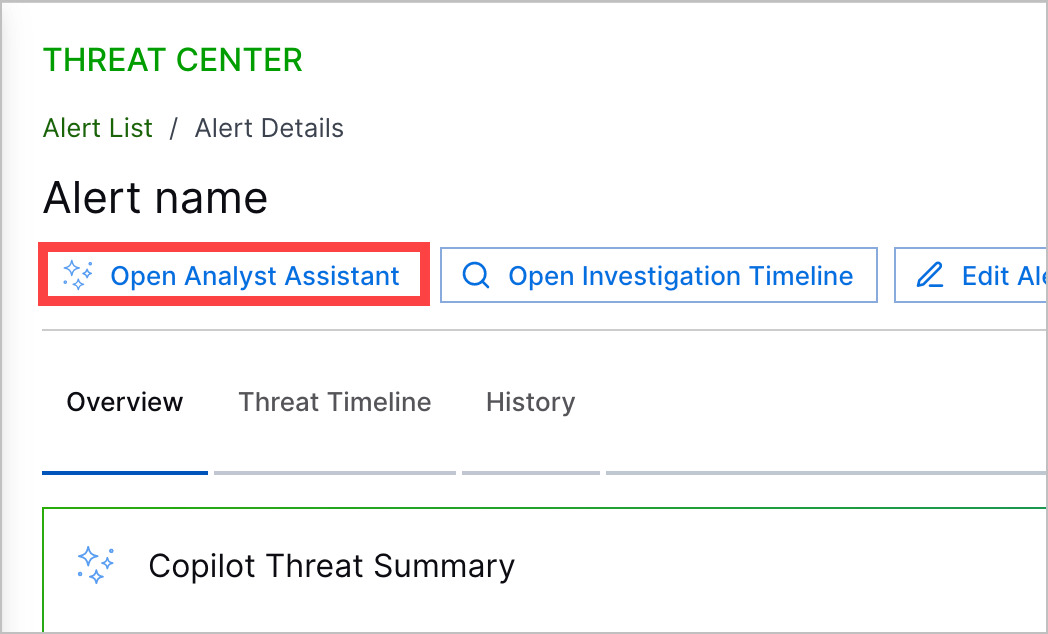
In Copilot Analyst Assistant, enter a prompt, then press return or Enter or click
 .
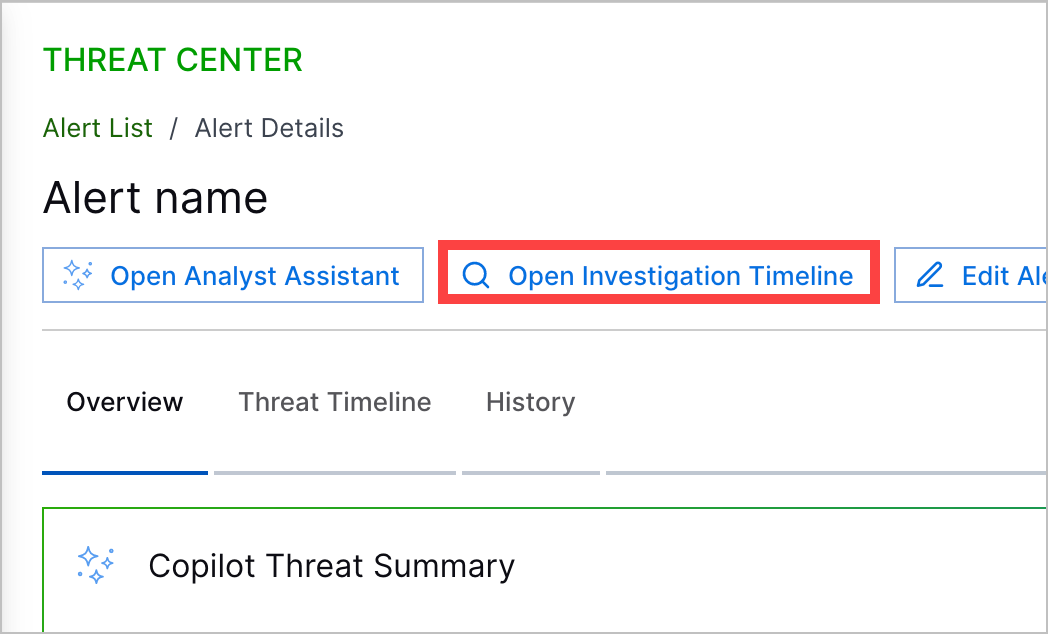
.Deepen your triage in Search and view all events associated with the attribute by which detections are grouped. To navigate directly to these events in the Search timeline view, click Open Investigation Timeline.
To respond to the alert, create a case from the alert.
[6] MITRE ATT&CK and ATT&CK are trademarks of The MITRE Corporation ("MITRE"). Exabeam is not affiliated with or sponsored or endorsed by MITRE. Nothing herein is a representation of the views or opinions of MITRE or its personnel.