- Onboard Cloud Collectors
- Shareable Service Accounts
- Add Accounts for AWS Cloud Collectors
- Add Accounts for Cisco Duo Cloud Collector
- Add Accounts for Google Cloud Collectors
- Add Accounts for Microsoft Cloud Collectors
- Add Accounts for Okta Cloud Collectors
- Add Accounts for Salesforce Cloud Collectors
- Add Accounts for Splunk Cloud Collectors
- Add Accounts for Trend Micro Cloud Collectors
- Add Accounts for Wiz
- Abnormal Security Cloud Collector
- Anomali Cloud Collector
- AWS CloudTrail Cloud Collectors
- AWS CloudWatch Cloud Collector
- AWS CloudWatch Alarms Cloud Collector
- AWS GuardDuty Cloud Collector
- AWS S3 Cloud Collector
- AWS Security Lake Cloud Collector
- AWS SQS Cloud Collector
- Azure Activity Logs Cloud Collector
- Azure Blob Storage Cloud Collector
- Azure Log Analytics Cloud Collector
- Azure Event Hub Cloud Collector
- Azure Storage Analytics Cloud Collector
- Azure Virtual Network Flow Cloud Collector
- Box Cloud Collector
- Broadcom Carbon Black Cloud Collector
- Cato Networks Cloud Collector
- ChatGPT Enterprise Cloud Collector
- Cisco Duo Cloud Collector
- Cisco Meraki Cloud Collector
- Cisco Secure Endpoint Cloud Collector
- Cisco Umbrella Cloud Collector
- Cloudflare Cloud Collector
- Cribl Cloud Collector
- CrowdStrike Cloud Collectors
- Cylance Protect (now Arctic Wolf) Cloud Collector
- DataBahn Cloud Collector
- Dropbox Cloud Collector
- GCP Cloud Logging Cloud Collector
- GCP Pub/Sub Cloud Collector
- GCP Security Command Center Cloud Collector
- Gemini Enterprise Cloud Collector
- GitHub Cloud Collector
- Gmail BigQuery Cloud Collector
- Google Workspace Cloud Collector
- Google Workspace Context Cloud Collector
- LastPass Cloud Collector
- Microsoft Copilot Integration
- Microsoft Defender XDR (via Azure Event Hub) Cloud Collector
- Microsoft Entra ID Context Cloud Collector
- Microsoft Entra ID Logs Cloud Collector
- Microsoft 365 Exchange Admin Reports Cloud Collector
- Supported Sources from Microsoft 365 Exchange Admin Reports
- Migrate to the Microsoft 365 Exchange Admin Reports Cloud Collector
- Prerequisites to Configure the Microsoft 365 Exchange Admin Reports Cloud Collector
- Configure the Microsoft 365 Exchange Admin Reports Cloud Collector
- Troubleshooting the Microsoft 365 Exchange Admin Reports Cloud Collector
- Microsoft 365 Management Activity Cloud Collector
- Microsoft Security Alerts Cloud Collector
- Microsoft Sentinel (via Event Hub) Cloud Collector
- Mimecast Cloud Collector
- Mimecast Incydr Cloud Collector
- Netskope Alerts Cloud Collector
- Netskope Events Cloud Collector
- Okta Cloud Collector
- Okta Context Cloud Collector
- Palo Alto Networks Cortex Data Lake Cloud Collector
- Palo Alto Networks XDR Cloud Collector
- Phishing Email Inbox Cloud Collector
- PingOne Identity Cloud Collector
- Progress ShareFile Cloud Collector
- Proofpoint On-Demand Cloud Collector
- Proofpoint Targeted Attack Protection Cloud Collector
- Qualys Cloud Collector
- Recorded Future Cloud Collector
- Recorded Future Context Cloud Collector
- Rest API Cloud Collector
- S2W Threat Intelligence Cloud Collector
- Salesforce Cloud Collector
- Salesforce EventLog Cloud Collector
- SentinelOne Alerts Cloud Collector
- SentinelOne Cloud Funnel Cloud Collector
- SentinelOne Threats Cloud Collector
- SentinelOne Cloud Collector
- ServiceNow Cloud Collector
- Slack Cloud Collector
- Snowflake Cloud Collector
- Sophos Central Cloud Collector
- Splunk Cloud Collector
- STIX/TAXII Cloud Collector
- Symantec Endpoint Security Cloud Collector
- Tenable Cloud Collector
- Trend Vision One Cloud Collector
- Trellix Endpoint Security Cloud Collector
- Vectra Cloud Collector
- Webhook Cloud Collectors
- Wiz API Cloud Collector
- Workday Cloud Collector
- Zoom Cloud Collector
- Zscaler ZIA Cloud Collector
- Shareable Service Accounts
CrowdStrike Falcon (via FDR) Cloud Collector
Migrate to the CrowdStrike Falcon (via FDR) Cloud Collector
With Exabeam Cloud Collectors, the CrowdStrike Falcon (via FDR) Cloud Collector is now available for the New-Scale Security Operations Platform. The new cloud collector enables you to ingest logs into the New-Scale Security Operations Platform and use the Exabeam Search to find specific events in those logs. Migration to the new app is recommended.
If you previously used the early access CrowdStrike Falcon (via S3) Cloud Connector, and want to take advantage of the new Cloud Collectors service, you must first migrate the SaaS cloud connector. Before you migrate, consider the following:
License Requirements: No additional license is required. The Cloud Collectors app is included with your existing license.
SaaS Cloud Connectors Support: Both the SaaS Cloud Connectors and the new Cloud Collectors environments can run in parallel.
The following table displays that the CrowdStrike Cloud Connector's FDR Items Explorer endpoint and endpoint-fdr are mapped to the new Cloud Collector CrowdStrike Falcon (via FDR).
Legacy Connector | Legacy Endpoint | New Collector |
|---|---|---|
CrowdStrike |
| CrowdStrike Falcon (via FDR) |
To migrate to the CrowdStrike Falcon (via FDR) Cloud Collector, use the following steps:
Log in to the New-Scale Security Operations Platform with your registered credentials as an administrator.
Navigate to Collectors > SaaS Cloud Connectors.
Note
To use the Migrate functionality, ensure that you have Exabeam Cloud Connectors version 2.5.483 or a later version.
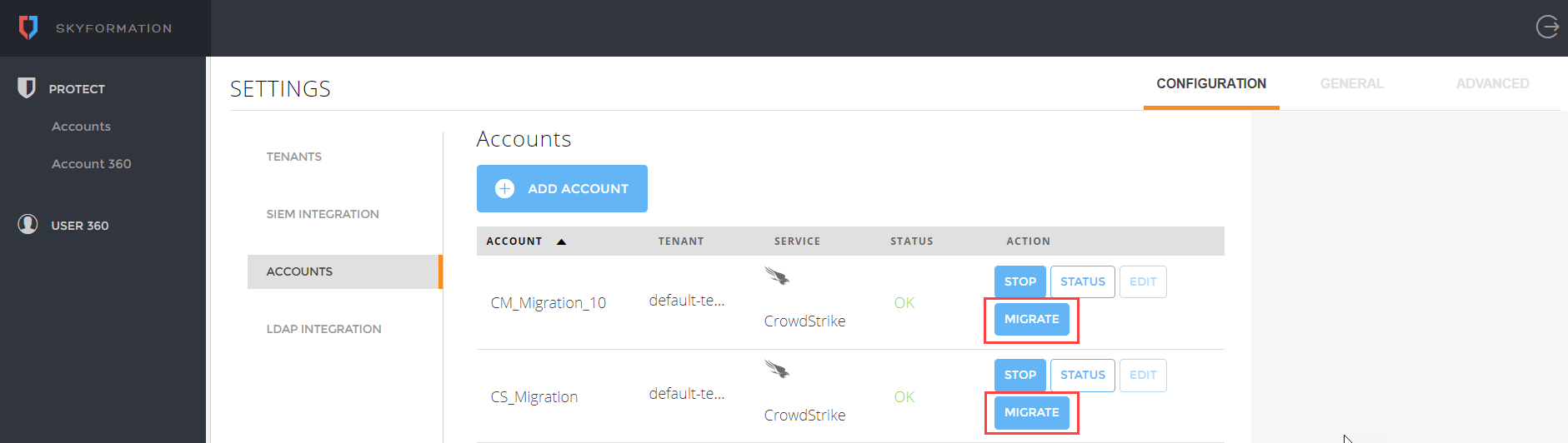
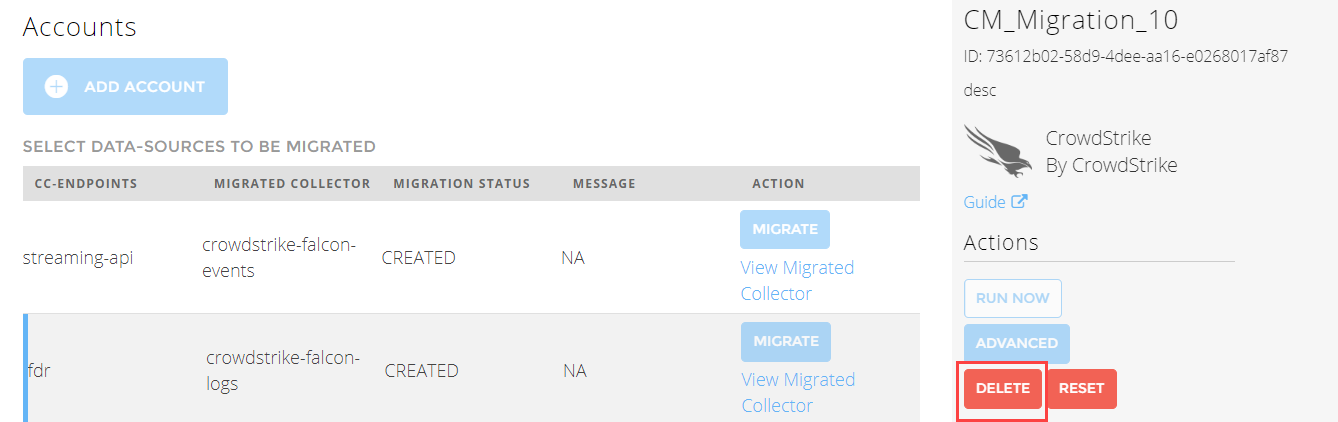
On the SaaS Cloud Connectors platform, navigate to Settings > Accounts.
Click Migrate for the CrowdStrike account that you want to migrate to the Cloud Collectors service.
Click Migrate for the endpoint that you want to migrate: streaming-api or fdr.
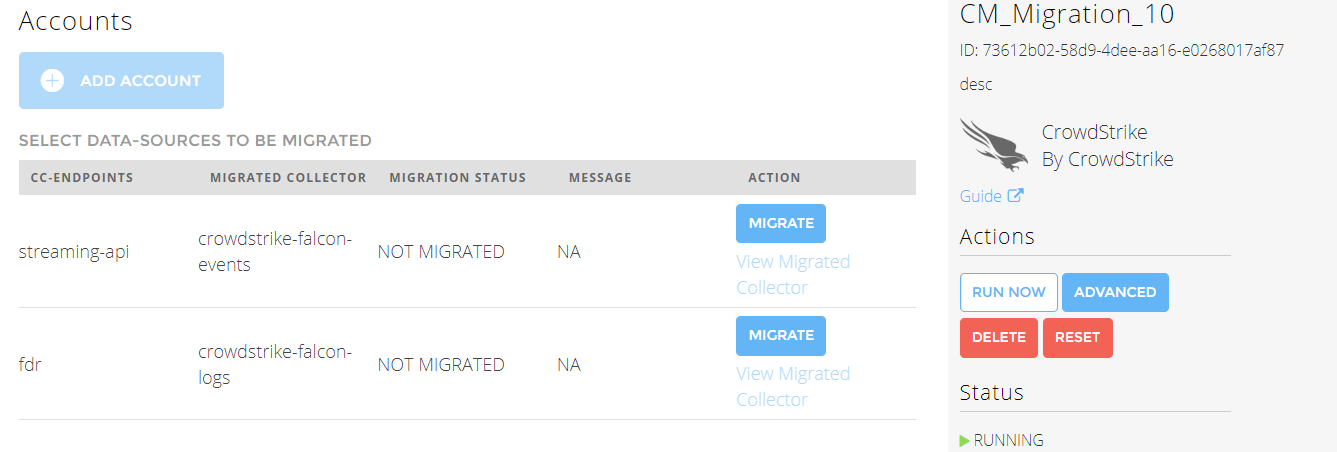
After you click Migrate, a cloud connector is migrated to Cloud Collectors on New-Scale Security Operations Platform .
To view the migrated connector, click View Migrated Collector.
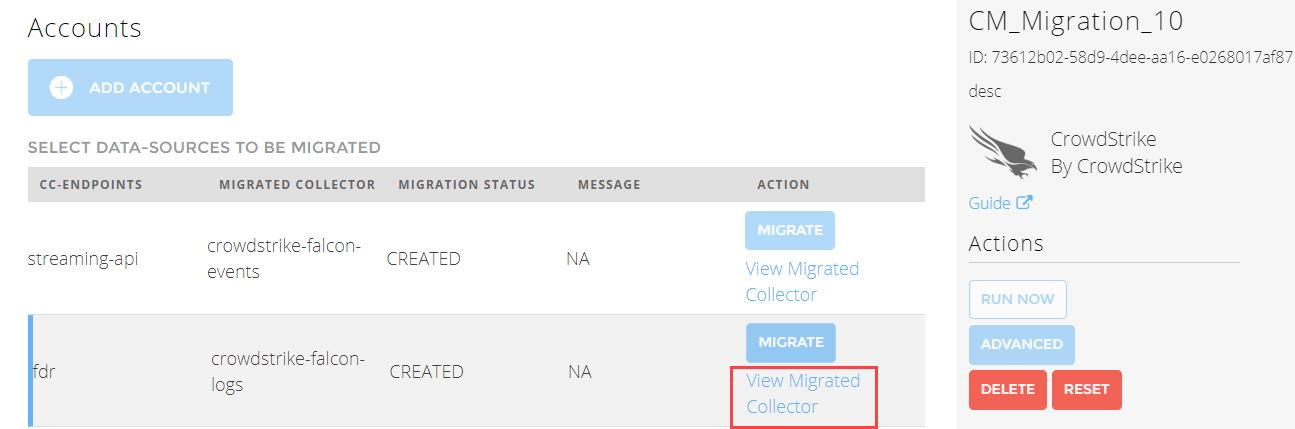
The migrated CrowdStrike Cloud Collector is ready to ingest data.
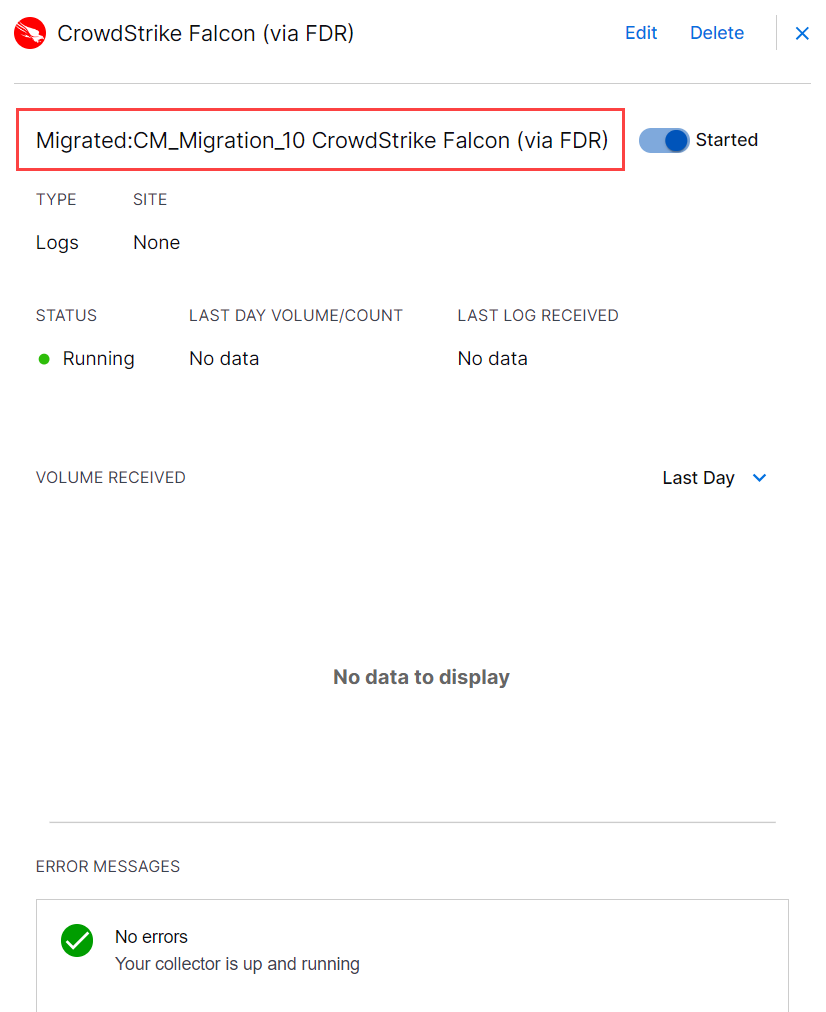
Verify if the migrated CrowdStrike Cloud Collector instance is running smoothly by checking the status of the cloud collector.
If you see any errors, refer to the Error Messages section for resolution or contact Exabeam support. If errors persist and you want to use the old SaaS cloud connector, delete the newly migrated CrowdStrike Cloud Collector instance on the New-Scale Security Operations Platform and continue to use the SaaS cloud connector.
After successful migration, if the newly migrated CrowdStrike Cloud Collector runs smoothly, consider deleting the old CrowdStrike Cloud Connector on the SaaS Cloud Connectors platform to avoid event duplication.
.
Prerequisites to Configure the CrowdStrike Falcon (via FDR) Cloud Collector
CrowdStrike supports Falcon Data Replicator (FDR) to retrieve events. FDR provides raw event data. Contact CrowdStrike support to obtain a managed AWS S3 bucket for storage for a short duration and Simple Queue Service (SQS) for notifications about newly created files. CrowdStrike support will provide you with Access Key, Access Secret, SQS region, and SQS URL.
Before you configure the CrowdStrike Falcon collector you must complete the following prerequisites:
Ensure that the https://*.crowdstrike.com service is open for communication with the New-Scale Security Operations Platform.
Make sure that you have Admin privileges for the Falcon platform and paid membership for Falcon Insight and Falcon Prevent products.
Contact CrowdStrike support to obtain the cloud endpoint API gateway assigned to your API client.
Note
CrowdStrike assigns a cloud endpoint, also called an API gateway, to each API client. For example: https://api.crowdstrike.com or https://api.us-2.crowdstrike.com.
Obtain Access Key, Access Secret, SQS region, and SQS URL. Contact CrowdStrike support to request a managed AWS S3 bucket for short-term storage and an SQS for new file notifications. Obtain the Access Key, Access Secret, SQS region, and SQS URL from the CrowdStrike support team.
Proceed to Configure the CrowdStrike Falcon (via FDR) Cloud Collector.
Configure the CrowdStrike Falcon (via FDR) Cloud Collector
The CrowdStrike Falcon (via FDR) Cloud Collector collects the data stored in S3 bucket to ingest data in the New-Scale Security Operations Platform.
To configure the CrowdStrike Falcon (via FDR) Cloud Collector:
Complete the prerequisites to configure the CrowdStrike Falcon (via FDR) Cloud Collector.
Log in to the New-Scale Security Operations Platform with your registered credentials as an administrator.
Navigate to Collectors > Cloud Collectors.
Click New Collector.
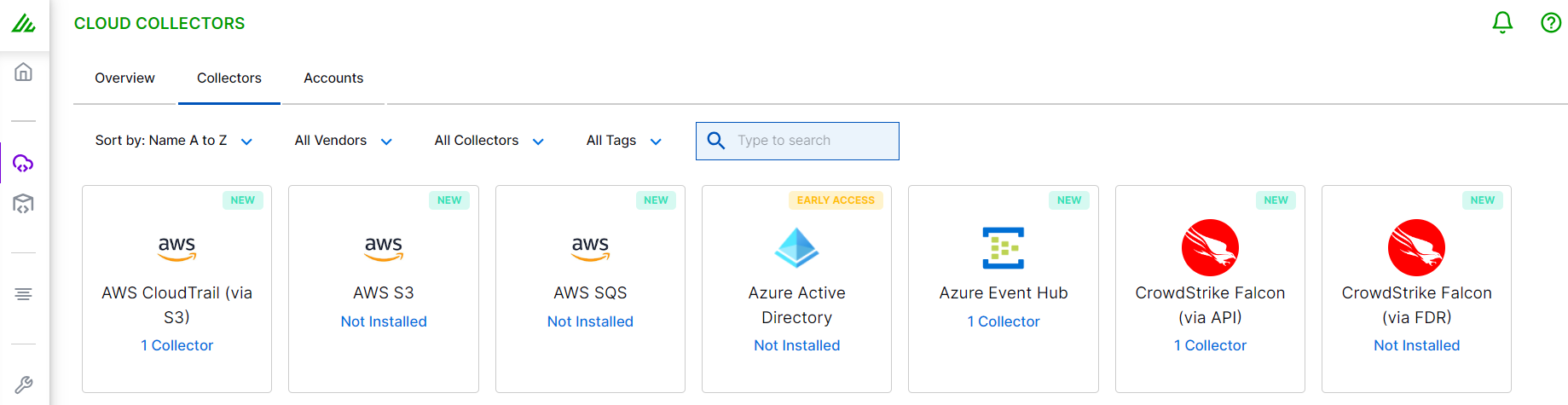
Click CrowdStrike Falcon (via FDR).
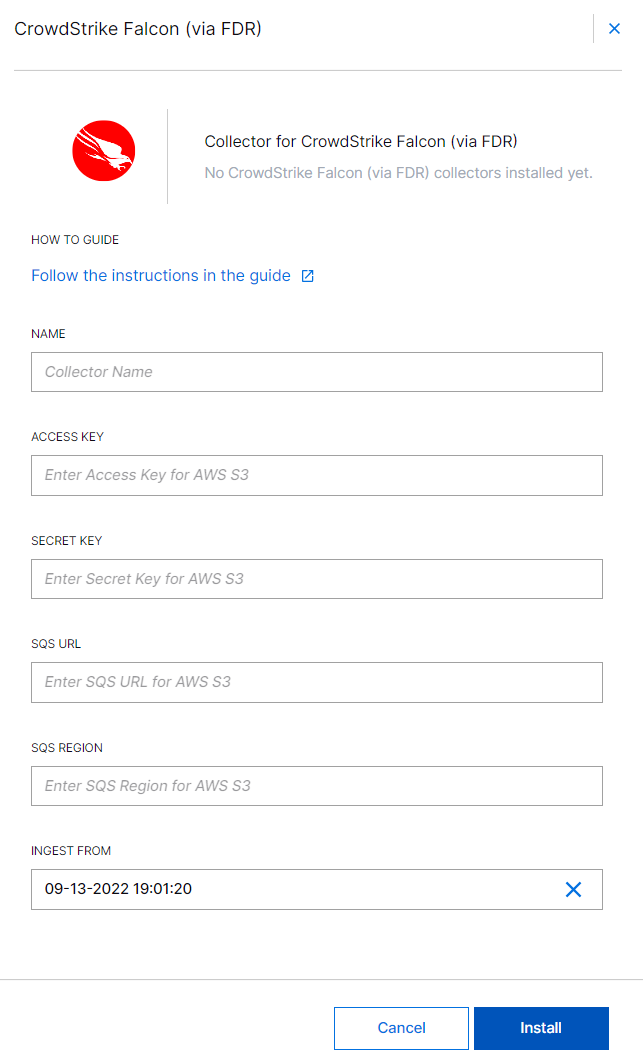
Specify a name for the Cloud Collector instance.
Enter the Access Key and Secret Key that you obtained from CrowdStrike support while completing the prerequisites.
Select the SQS region. For example,
us-west-1.In the Ingest From field, select the time and date to provide a threshold before which the collector will exclude events. If you leave this field blank and do not provide a threshold, all logs are ingested.
(Optional) SITE – Select an existing site or to create a new site with a unique ID, click manage your sites. Adding a site name helps you to ensure efficient management of environments with overlapping IP addresses.
By entering a site name, you associate the logs with a specific independent site. A sitename metadata field is automatically added to all the events that are going to be ingested via this collector. For more information about Site Management, see Define a Unique Site Name.
(Optional) TIMEZONE – Select a time zone applicable to you for accurate detections and event monitoring.
By entering a time zone, you override the default log time zone. A timezone metadata field is automatically added to all events ingested through this collector.
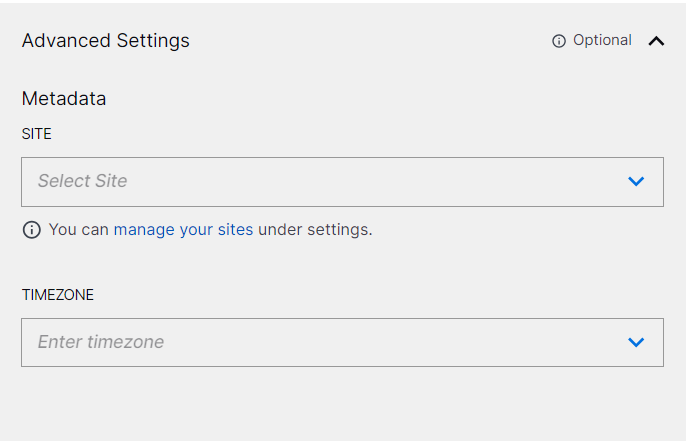
A cloud collector determines whether Daylight Saving Time (DST) is active based on the current date and automatically adjusts the time by adding or subtracting one hour, ensuring more accurate time reporting.
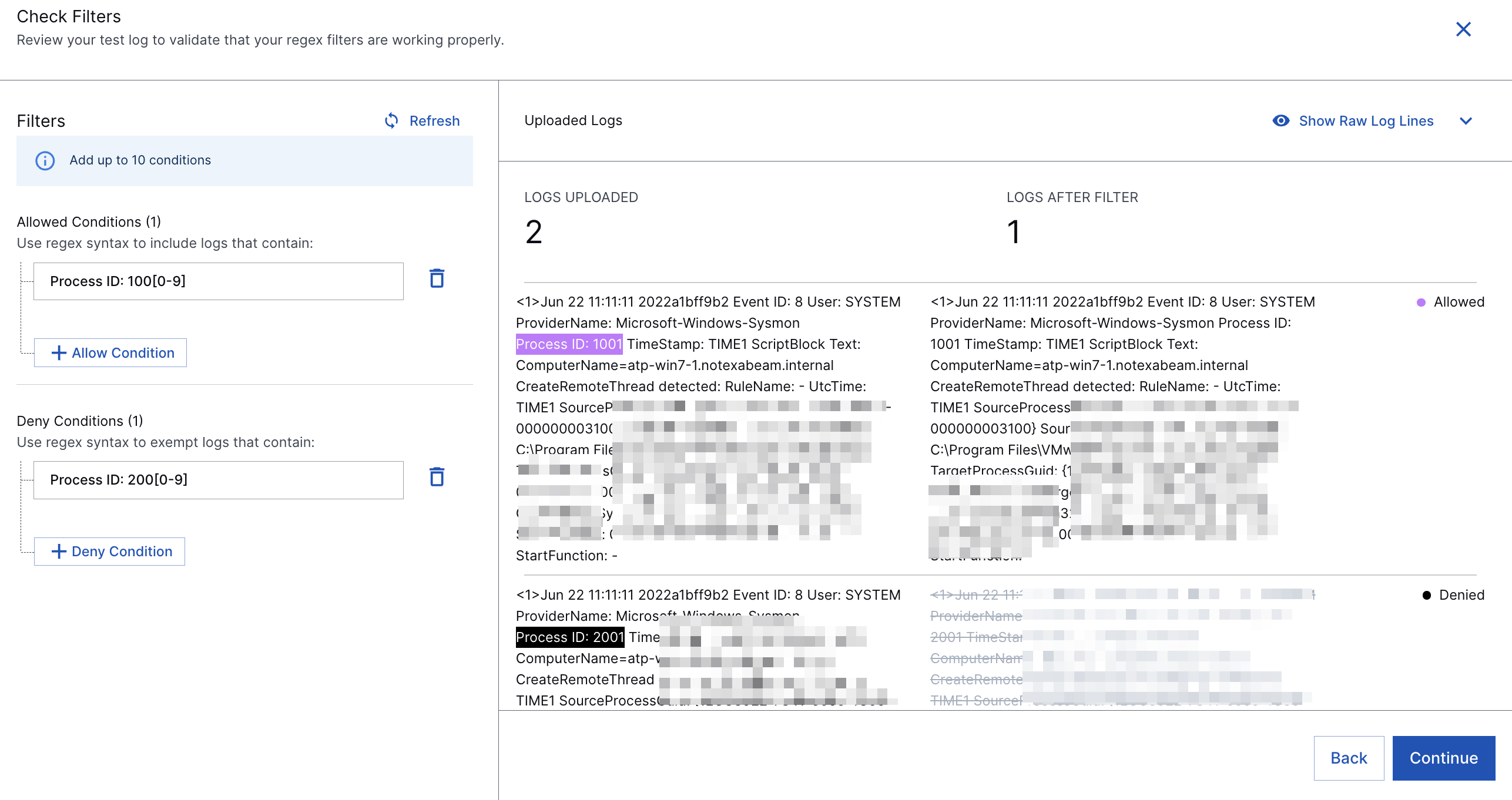
(Optional) Add filter conditions using regex syntax to include and exempt logs.
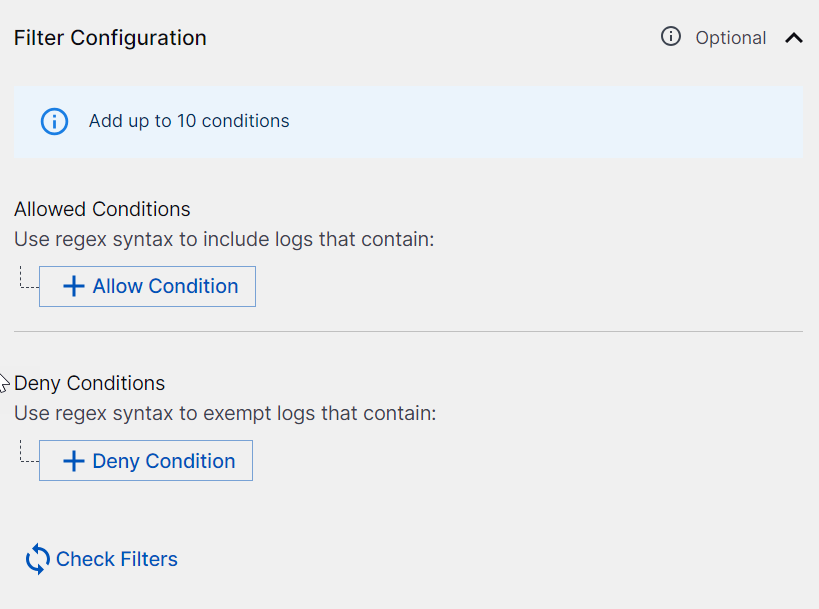
In the Allowed Conditions section, add conditions to include logs to be sent to the New-Scale Security Operations Platform.
For example, for EventCode that matches 100X, use the Allowed Condition
EventCode=100[0-9].Raw log:
LogName=Application EventCode=1001 EventType=4 ComputerName=windows-splunk-forwarder-vp-23 SourceName=Windows Error Reporting Type=Information RecordNumber=168946846 Keywords=Classic TaskCategory=None OpCode=Info Message=Fault bucket , type 0 Event Name: APPCRASH Response: Not available Cab Id: 0
In the Deny Conditions section, add conditions for the logs that you don't want to send to the New-Scale Security Operations Platform.
For example, if you don't want to include eventType between 1 and 5, use the Deny Condition
EventType=[1-5].Raw log:
LogName=Application EventCode=1001 EventType=4 ComputerName=windows-splunk-forwarder-vp-23 SourceName=Windows Error Reporting Type=Information RecordNumber=168946846 Keywords=Classic TaskCategory=None OpCode=Info Message=Fault bucket , type 0 Event Name: APPCRASH Response: Not available Cab Id: 0
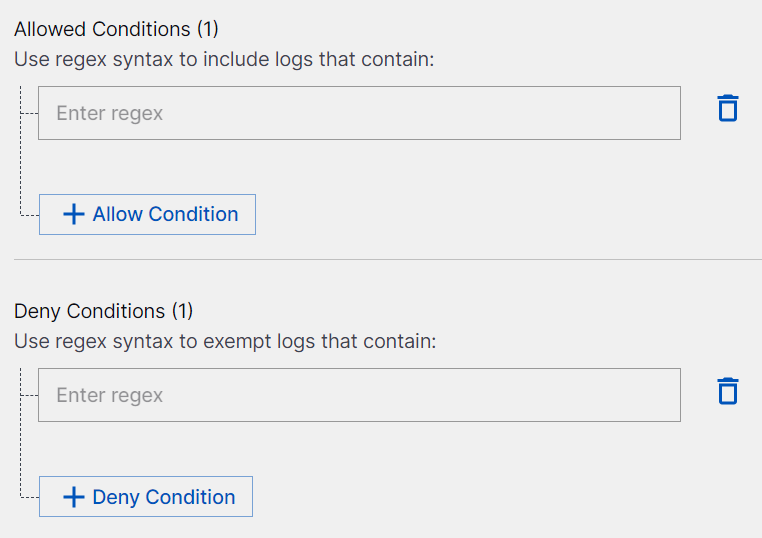
Caution
Enter a valid regex syntax. Do not enter
.*or.+at the start or at the end of the regex syntax.Use
.*or.+only if required, in the middle of the regex syntax after adding?next to each of these characters. For example,.*?.Do not use these prefixes
^.*, ^.+, ^.*?, ^.+?and suffixes.*$, .+$, .*?$, .+?$.
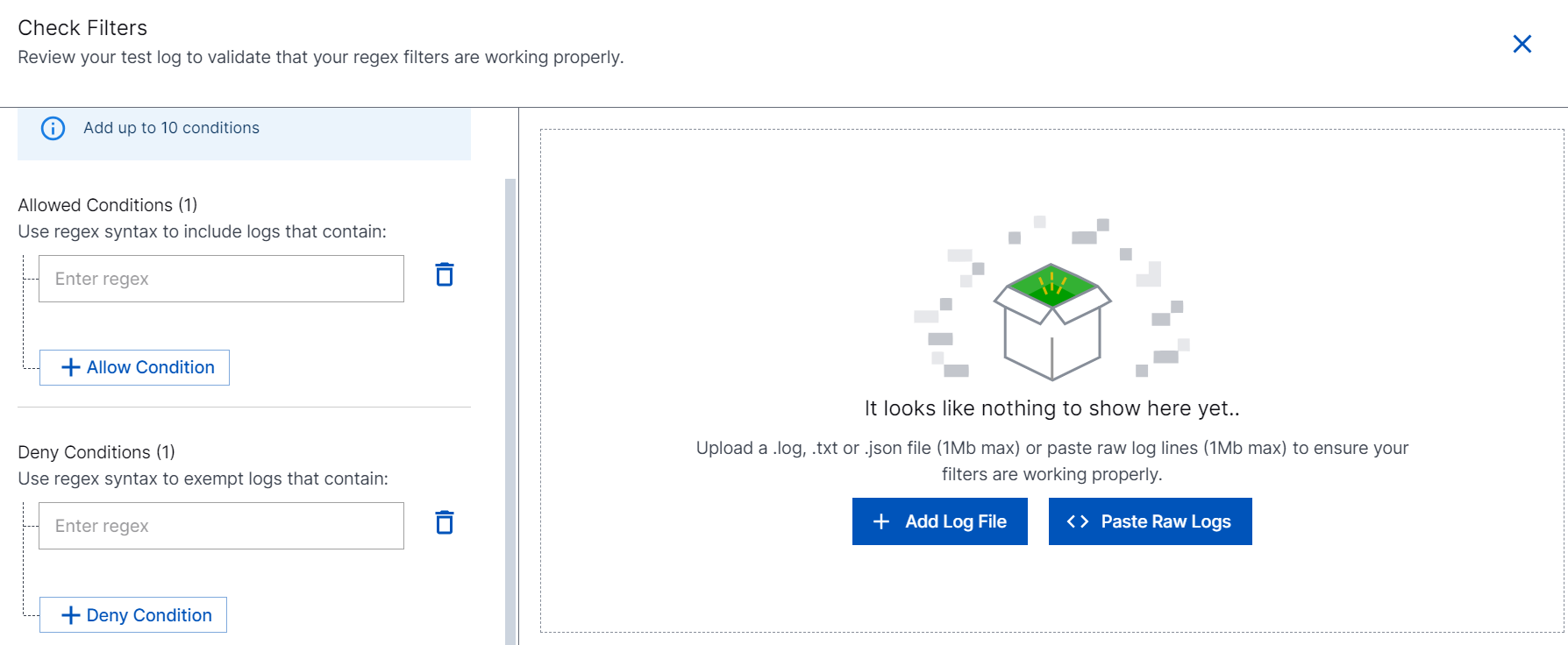
Click Check Filters to verify if the filters are providing the correct results. Then, add log files or paste raw logs in the right pane to verify if the filters that you set are working appropriately.
Click Import.
If you specify the Allowed and Deny conditions, the cloud collector processes logs based on your conditions. Ensure that the regex pattern that you specify is valid.
Refer to the following screenshot as an example of the logs that are processed based on the Allowed and Deny conditions.
Note
Using egress filters affects the performance of the collector and decreases overall EPS. The more you set complex filters, the bigger impact you will observe on the collector performance. For example with three filters, overall EPS can decrease approximately by 15% to 20% based on the filter complexity.
To confirm that the New-Scale Security Operations Platform communicates with the service, click Test Connection.
Click Install.
A confirmation message informs you that the new collector is created.
