- Onboard Cloud Collectors
- Shareable Service Accounts
- Add Accounts for AWS Cloud Collectors
- Add Accounts for Cisco Duo Cloud Collector
- Add Accounts for Google Cloud Collectors
- Add Accounts for Microsoft Cloud Collectors
- Add Accounts for Okta Cloud Collectors
- Add Accounts for Salesforce Cloud Collectors
- Add Accounts for Splunk Cloud Collectors
- Add Accounts for Trend Micro Cloud Collectors
- Add Accounts for Wiz
- Abnormal Security Cloud Collector
- Anomali Cloud Collector
- AWS CloudTrail Cloud Collectors
- AWS CloudWatch Cloud Collector
- AWS CloudWatch Alarms Cloud Collector
- AWS GuardDuty Cloud Collector
- AWS S3 Cloud Collector
- AWS Security Lake Cloud Collector
- AWS SQS Cloud Collector
- Azure Activity Logs Cloud Collector
- Azure Blob Storage Cloud Collector
- Azure Log Analytics Cloud Collector
- Azure Event Hub Cloud Collector
- Azure Storage Analytics Cloud Collector
- Azure Virtual Network Flow Cloud Collector
- Box Cloud Collector
- Broadcom Carbon Black Cloud Collector
- Cato Networks Cloud Collector
- ChatGPT Enterprise Cloud Collector
- Cisco Duo Cloud Collector
- Cisco Meraki Cloud Collector
- Cisco Secure Endpoint Cloud Collector
- Cisco Umbrella Cloud Collector
- Cloudflare Cloud Collector
- Cribl Cloud Collector
- CrowdStrike Cloud Collectors
- Cylance Protect (now Arctic Wolf) Cloud Collector
- DataBahn Cloud Collector
- Dropbox Cloud Collector
- GCP Cloud Logging Cloud Collector
- GCP Pub/Sub Cloud Collector
- GCP Security Command Center Cloud Collector
- Gemini Enterprise Cloud Collector
- GitHub Cloud Collector
- Gmail BigQuery Cloud Collector
- Google Workspace Cloud Collector
- Google Workspace Context Cloud Collector
- LastPass Cloud Collector
- Microsoft Copilot Integration
- Microsoft Defender XDR (via Azure Event Hub) Cloud Collector
- Microsoft Entra ID Context Cloud Collector
- Microsoft Entra ID Logs Cloud Collector
- Microsoft 365 Exchange Admin Reports Cloud Collector
- Supported Sources from Microsoft 365 Exchange Admin Reports
- Migrate to the Microsoft 365 Exchange Admin Reports Cloud Collector
- Prerequisites to Configure the Microsoft 365 Exchange Admin Reports Cloud Collector
- Configure the Microsoft 365 Exchange Admin Reports Cloud Collector
- Troubleshooting the Microsoft 365 Exchange Admin Reports Cloud Collector
- Microsoft 365 Management Activity Cloud Collector
- Microsoft Security Alerts Cloud Collector
- Microsoft Sentinel (via Event Hub) Cloud Collector
- Mimecast Cloud Collector
- Mimecast Incydr Cloud Collector
- Netskope Alerts Cloud Collector
- Netskope Events Cloud Collector
- Okta Cloud Collector
- Okta Context Cloud Collector
- Palo Alto Networks Cortex Data Lake Cloud Collector
- Palo Alto Networks XDR Cloud Collector
- Phishing Email Inbox Cloud Collector
- PingOne Identity Cloud Collector
- Progress ShareFile Cloud Collector
- Proofpoint On-Demand Cloud Collector
- Proofpoint Targeted Attack Protection Cloud Collector
- Qualys Cloud Collector
- Recorded Future Cloud Collector
- Recorded Future Context Cloud Collector
- Rest API Cloud Collector
- S2W Threat Intelligence Cloud Collector
- Salesforce Cloud Collector
- Salesforce EventLog Cloud Collector
- SentinelOne Alerts Cloud Collector
- SentinelOne Cloud Funnel Cloud Collector
- SentinelOne Threats Cloud Collector
- SentinelOne Cloud Collector
- ServiceNow Cloud Collector
- Slack Cloud Collector
- Snowflake Cloud Collector
- Sophos Central Cloud Collector
- Splunk Cloud Collector
- STIX/TAXII Cloud Collector
- Symantec Endpoint Security Cloud Collector
- Tenable Cloud Collector
- Trend Vision One Cloud Collector
- Trellix Endpoint Security Cloud Collector
- Vectra Cloud Collector
- Webhook Cloud Collectors
- Wiz API Cloud Collector
- Workday Cloud Collector
- Zoom Cloud Collector
- Zscaler ZIA Cloud Collector
- Shareable Service Accounts
Prerequisites to Configure the Phishing Email Inbox Cloud Collector
Before you configure the Phishing Email Inbox cloud collector you must complete the following prerequisites:
Note the phishing email address which is a dedicated internal email address of your organization, used for reporting suspicious email messages.
Complete the following prerequisite tasks for the mailbox type Outlook.
Complete the following prerequisite tasks for the mailbox type Gmail.
Create and Register a Microsoft Entra ID Application
Log into your Azure account by accessing the Azure portal.
From the available Azure Services, select Microsoft Entra ID.
From the left navigation pane, select App Registrations, then click New registration.
On the Register an application page, enter the following information:
Name – Specify a name for the new application. For example, Exabeam MS Entra ID App.
Supported account types – Select the account type Accounts in this organizational directory only.
Redirect URI – (Optional) Select the Web platform and specify a URI.
Click Register. When registration is complete, the Overview tab of the new application is displayed.
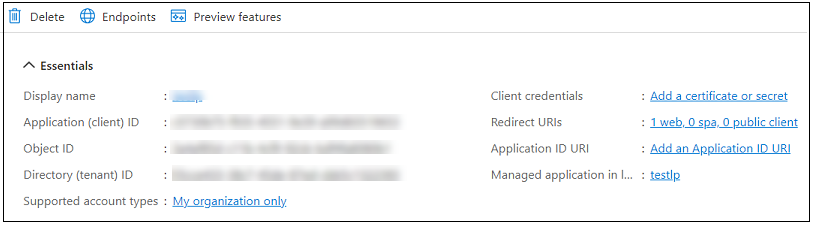
Copy and make a note of the values for both the Application (client) ID and the Directory (tenant) ID. You will need these values when configuring a cloud collector.
Assign API Permissions
Use the following steps to assign the required permission to the Microsoft Entra ID application.
In your new Microsoft Entra ID application, click API permissions in the left navigation pane.
Click Add a permission.
In the Request API permissions pane on the right, click the APIs my organization uses tab.
Use the search field to find and select a Office 365 Exchange Online.
Click Application permissions to expand the permission selections.
In the permissions search bar, search for and expand a specific set of permissions. In the expanded options, select the permissions you need. For the Phishing Email Inbox cloud collector, select IMAP.AccessAsApp.
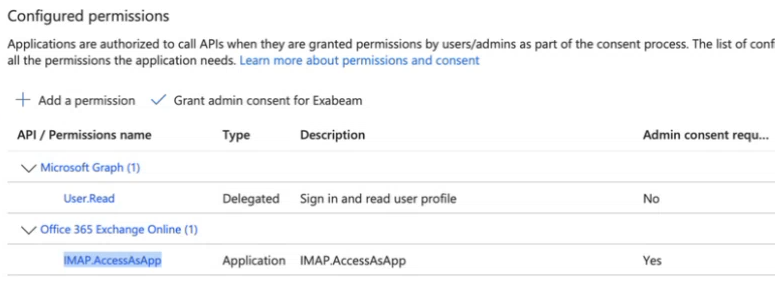
Click Add permissions. The new permission is added to the application.
Provide admin consent for all application permissions. Then, register the application's service principal in Exchange Online by running these PowerShell commands for Installing ExchangeOnline.
Install ExchangeOnlineManagement Install-Module -Name ExchangeOnlineManagement -Scope CurrentUser Import-Module ExchangeOnlineManagement Connect-ExchangeOnline
Run the following command to check if IMAP is enabled for the email address.
Get-CASMailbox -Identity <email_address> | Select IMAPEnabled
For example, Get-CASMailbox -Identity [email protected] | Select IMAPEnabled
Run the following command to register Service Principal in Exchange. Enter the App ID and the Service ID in the command. The App ID is the client ID and the Service ID is the Object ID from enterprise application.
New-ServicePrincipal -AppId e123456a-1234-11dd-1234-1234a65d11ad -ServiceId 1234f11e-afc2-1234-aa11-77fd4ad11c30
Get-ServicePrincipal | fl
Add-MailboxPermission -Identity "[email protected]" -User <SERVICE_PRINCIPAL_ID> -AccessRights FullAccess
Generate Certificates and Secrets
In your new Microsoft Entra ID application, click Certificates & secrets in the left navigation pane.
Use the authentication method OAuth2 and select the Client secrets tab, and continue with the next step.
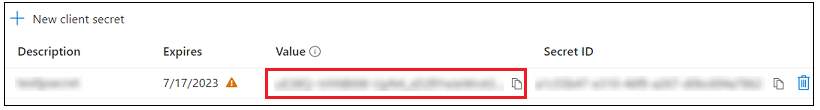
On the Client Secrets tab, click New client secret and do the following:
Enter a Description and an Expires term for the secret.
Click Add. The new client secret is displayed on the Client secrets tab.
Copy and make a note of the Value. You will need this client secret value when you configure a Microsoft cloud collector. You will not be able to recover this value later if you don't make a note of it.
Grant Administration Consent
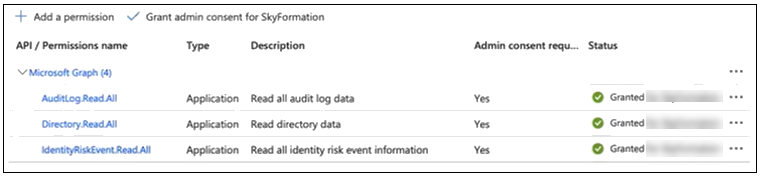
When all of the API permissions have been created, the configured permissions table should look like the image below. Notice that the Status for each new permission is Not granted.
In order for a Phishing Email Inbox cloud collector to pull data from these data sources, you must grant administration consent for each API permission as follows:
Above the configure permissions table, click Grant admin consent.
When prompted to confirm, click Yes. The Status for each permission changes to Granted.
Obtain the App Password for Gmail
Use the following steps to obtain app password for configuring the Phishing Email Inbox cloud collector with the mailbox type Gmail.
Access myaccount.google.com and navigate to your Google Account Setting page.
In the left pane, click Security & sign-in.
Enable 2-step verification and scroll to the App passwords section.
Specify a name for the app and click Create.
A password is generated and displayed on a pop-up box. Record the password for later use.
